IoT devices now outnumber traditional endpoints in most enterprise environments. From printers and cameras to medical equipment and building systems, these devices enable automation and efficiency — but they also expand the attack surface in ways traditional security tools were never designed to manage.
Portnox delivers cloud-native IoT security solutions that help organizations discover, identify, and control connected devices using agentless Network Access Control (NAC), zero trust principles, and continuous posture evaluation. This approach improves visibility, enforces least-privilege access, and reduces risk across modern IoT environments without adding operational complexity.

Many IoT devices were not built with enterprise-grade security in mind. Organizations commonly face IoT security risks such as:
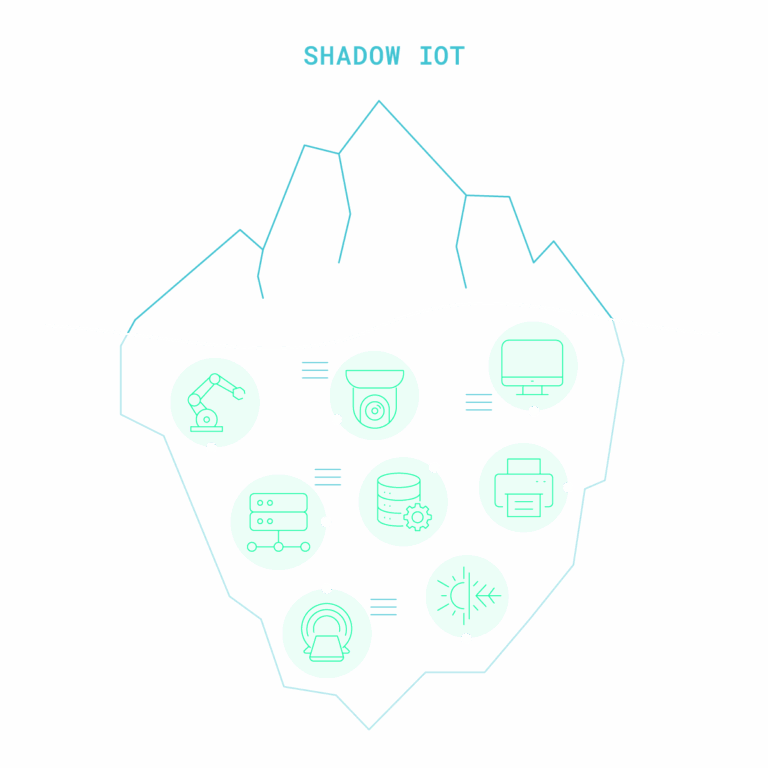
IoT devices are also frequently deployed outside of formal IT processes, creating Shadow IoT that operates beyond traditional security controls. These gaps make it difficult to detect unauthorized devices, enforce consistent access policies, or prevent lateral movement once a device is compromised.
Without effective IoT security controls, a single vulnerable device can provide attackers with a foothold into sensitive systems and data.
You cannot secure what you cannot see.
Portnox provides continuous, agentless visibility into every IoT device connecting to the network, including unmanaged and embedded devices that cannot support agents or traditional authentication methods. This visibility spans wired and wireless environments and delivers the context security teams need to assess risk in real time.
Using advanced fingerprinting and profiling, Portnox identifies:
This intelligence enables more accurate IoT device classification, faster threat detection, and informed access decisions based on actual device behavior rather than assumptions.


Visibility alone is not enough to secure IoT environments. Devices must be continuously evaluated and restricted to only the resources they are authorized to access.
Portnox enforces zero trust access control using cloud-native NAC built on industry standards such as 802.1X and RADIUS. When IoT devices attempt to connect, Portnox evaluates identity, device characteristics, and security posture before granting access — and continues to monitor compliance throughout the session.
With Portnox, organizations can:
Support for EAP-based authentication and certificate-based access allows organizations to eliminate shared credentials and apply stronger, identity-driven controls wherever devices support them. Continuous posture evaluation ensures trust is never static, aligning IoT security with zero trust principles.
Traditional IoT security platforms often depend on endpoint agents or on-premises appliances, which are impractical for embedded devices and difficult to scale.
Portnox is purpose-built for modern IoT environments:
By eliminating appliances and agents, Portnox enables organizations to secure IoT deployments quickly without disrupting operations or overburdening IT teams.


Portnox supports a wide range of IoT security use cases where visibility, access control, and compliance are critical:
These use cases demonstrate how agentless NAC and zero trust enforcement extend security to environments where traditional endpoint controls fall short.
Many legacy IoT and NAC platforms rely on appliance-based architectures that are costly to deploy, complex to manage, and slow to adapt to dynamic environments. These tools often prioritize visibility without delivering real-time enforcement or zero trust alignment.
Portnox delivers a modern alternative by providing:
This approach aligns IoT security with modern zero trust strategies and supports hybrid, distributed enterprise environments.

As IoT deployments continue to grow, organizations need security controls designed for scale, visibility, and unmanaged devices. Portnox delivers cloud-native IoT security that combines agentless discovery, access control, and automated enforcement — without agents or appliances.
Start your free 30-day trial or request a demo to see how Portnox secures IoT devices across modern enterprise networks.

Staying ahead in IT means strengthening cybersecurity—and zero trust architectures now lead the charge. But let’s face it: embracing zero trust can feel daunting. With so many tools and complexities, it’s easy to lose your way.
To understand how organizations navigate zero trust, Portnox teamed up with TechTarget. We surveyed hundreds of IT and cybersecurity professionals across North America. Discover the insights we uncovered in our Trends in Zero Trust report.

IoT security solutions protect connected devices and the networks they operate on by providing visibility, access control, and continuous monitoring. These capabilities help organizations reduce risk, prevent unauthorized access, and manage large volumes of unmanaged devices more securely.
IoT security is important because many connected devices lack strong built-in protections. When unmanaged, they can be exploited to access sensitive systems, move laterally across networks, or disrupt critical operations.
Common IoT security risks include unknown or unmanaged devices, weak or shared credentials, outdated firmware, limited monitoring, and lack of segmentation. These gaps increase exposure to unauthorized access and security incidents.
Network Access Control improves IoT security by verifying devices before granting access and enforcing segmentation and least-privilege policies. NAC limits what devices can access if compromised and enables continuous enforcement across the network.
Zero trust applies to IoT environments by requiring continuous verification of devices rather than assuming trust. Devices are granted only the minimum access required, reducing exposure and limiting the impact of compromise.
Portnox secures agentless IoT devices using network-based identification, fingerprinting, and NAC policy enforcement. This approach allows organizations to control access and monitor behavior without installing software on the device.
Yes. IoT security solutions that provide visibility, access control, and audit logging help organizations demonstrate alignment with regulatory and industry frameworks while improving overall security posture.
After completing the form, an email will be sent to you with the report download link.