COBIT, an industry-leading cybersecurity framework, provides comprehensive guidelines for effective IT governance and risk management. As organizations strive for COBIT compliance, Network Access Control (NAC) emerges as a crucial ally. NAC solutions bolster COBIT principles by enforcing strict access controls, validating user identities, and continuously monitoring network traffic. By implementing NAC, organizations fortify their security posture, mitigate risks, and ensure compliance with COBIT’s stringent cybersecurity requirements.
Controlling access is the first step to controlling risk when it comes to network security. Portnox Cloud helps enforce access control policies by allowing or denying network access based on predefined rules and policies. This supports the COBIT principle of ensuring that only authorized individuals have appropriate access to information and systems. Role-based access is a key component of the Portnox Cloud – make sure that resources are protected and accessed only by those who need them for their job function, and prevent lateral movement through the network in the event of a data breach.
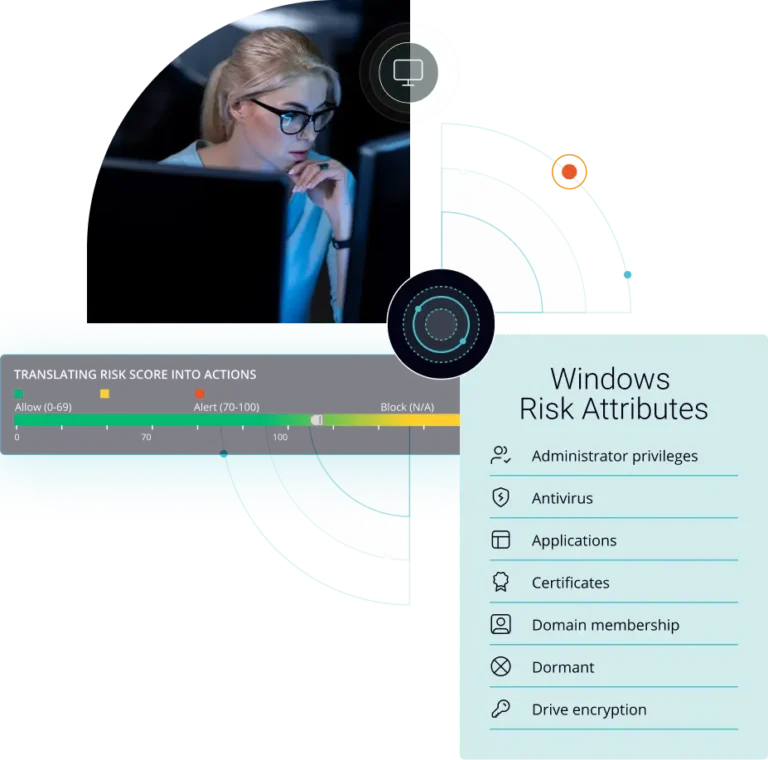
NAC can contribute to risk management efforts by enforcing security measures such as authentication, authorization, and endpoint compliance checks. This aligns with COBIT’s objective of identifying and managing cybersecurity risks to protect critical assets. The Portnox Cloud features a robust risk policy engine that assigns a risk score to a device based on your security policies and lets you take action to only allow those in compliance to access your network. And risk scores are continuously calculated, so if anything changes on a device it will be adjusted for immediate action to be taken.
NAC can help organizations meet compliance obligations by ensuring that devices accessing the network comply with security policies, such as having up-to-date antivirus software or applying necessary patches. Compliance with regulations and standards is a key aspect of COBIT’s governance objectives. The Portnox Cloud offers powerful automated remediation options beyond the traditional deny/allow/quarantine – if your antivirus is out of date we can update it, if your firewall is not running we can start it. Make sure user devices are compliant while taking the burden off your IT Team.
NAC solutions can provide real-time visibility into network activity and help detect and respond to security incidents promptly. This aligns with COBIT’s objective of establishing an effective incident response and management process. The Portnox Cloud utilizes RADIUS, the gold standard AAA protocol (Authentication, Authorization, and Accounting) so not only can you make sure that people have only the access they need to do their job, but you can keep track of who was where and when in the event of a data breach.
Network access control solutions traditionally deliver monitoring capabilities, such as logging and reporting on network access events. This information can be valuable for compliance audits and demonstrating adherence to security policies, which aligns with COBIT’s objective of monitoring and reporting on the effectiveness of controls. Portnox provides reporting and alerting along with integration into a wide variety of SIEM tools so you have all of the data you need about your network easily accessible when you need it.
NAC can integrate with Identity & Access Managemet (IAM) systems to enhance access control mechanisms and ensure that only authorized users and devices are granted network access. This supports the COBIT framework’s objective of establishing an effective identity-based access control policy enforcement mechanism. The Portnox Cloud of it’s own proprietary directory and integrates with a variety of IAM solutions, including Azure Active Directory, Google Workspace, JumpCloud, and Okta.
The COBIT framework provides a comprehensive set of IT governance and management best practices, which covers a broad spectrum of topics, including risk management, security, compliance, and performance management. Network access control is a key piece of meeting COBIT compliance, and the Portnox Cloud can help you get there. Learn more by downloading our product brief.
COBIT Compliance
After completing the form, an email will be sent to you with the report download link.