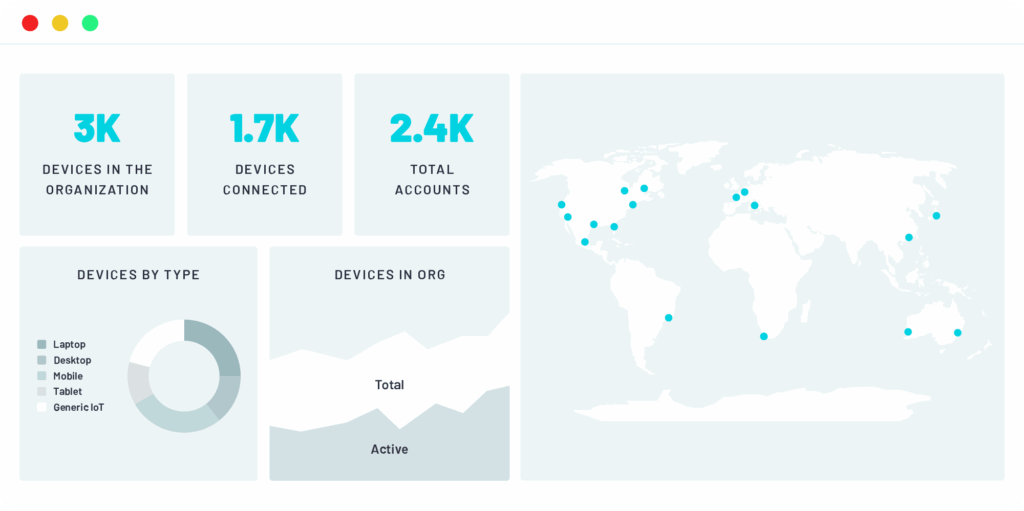
Gain real-time visibility of endpoints trying to connect to your network and infrastucture, plus additional context such as their location, device type, and requested access layer for authentication.
Extend zero trust security coverage to company devices, BYOD and IoT / OT alike, no matter if they’re authenticating via wired ports, WiFi or VPN.
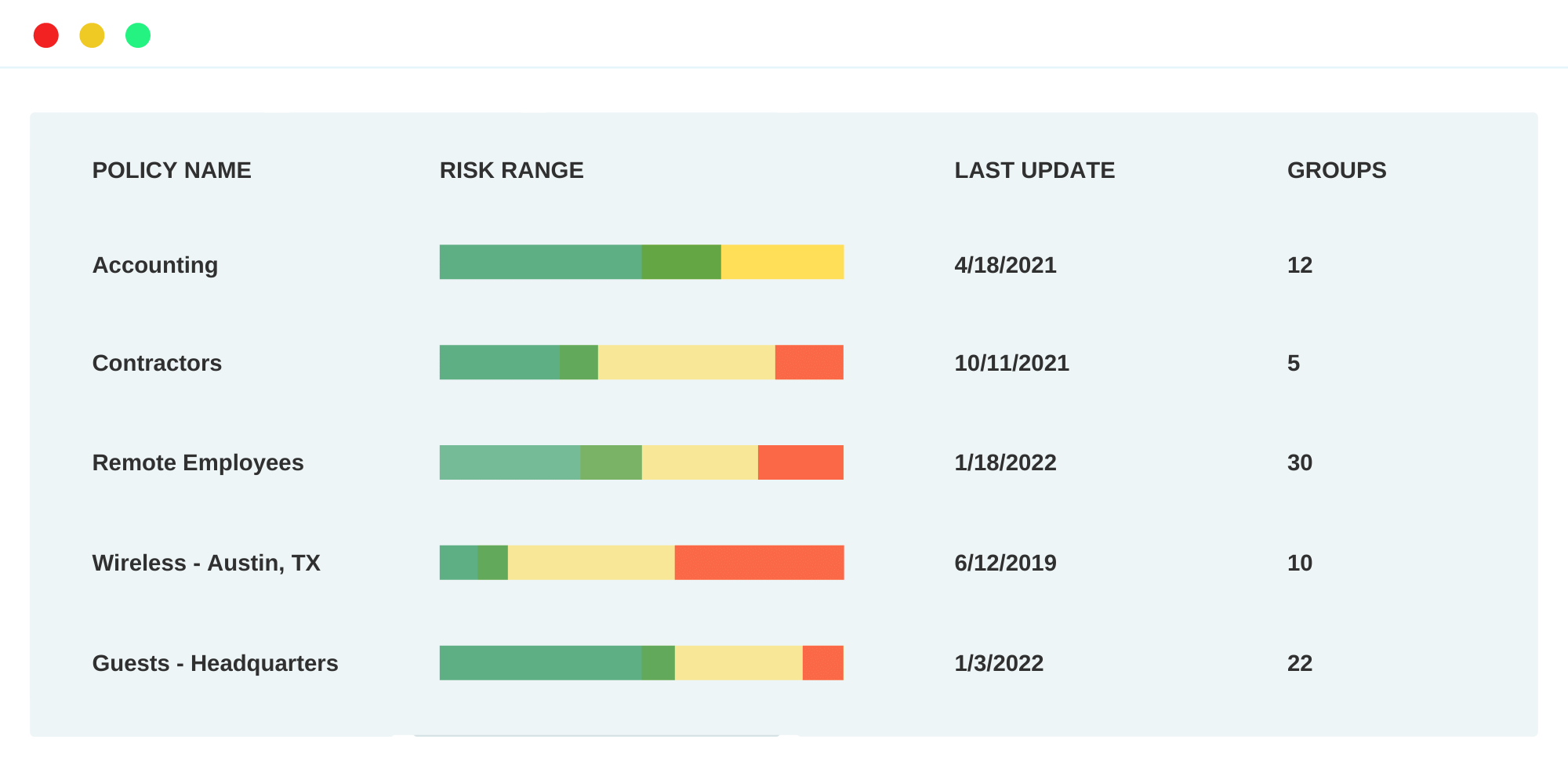
Define and enforce unique access control policies based on roles, locations, device types and more across your various network access layers.
Additionally, leverage Portnox Cloud’s powerful risk assessment policy configuration capabilities to continually monitor the risk posture of connected devices – including managed and BYOD – enabling your network administrators to understand the true zero trust security posture of the network at any point in time.
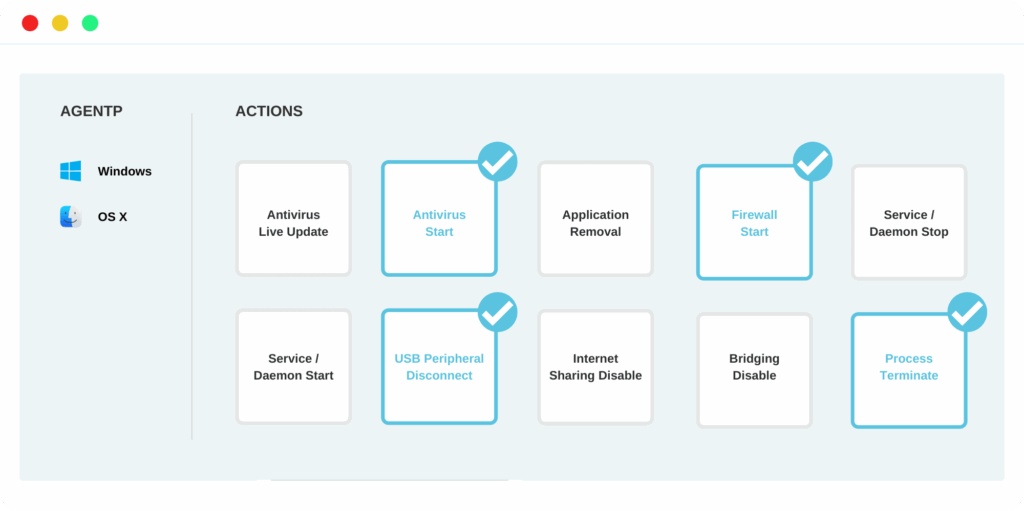
Quarantine vulnerable, non-compliant devices and return them to a healthy, compliant state automatically by setting unique endpoint remediation policies in accordance with your compliance requirements.
Portnox Cloud’s compliance enforcement capabilities can help your organization adhere to industry-specific regulatory and compliance standards such as HIPAA, GLBA, PCI DSS, GDPR and beyond.
Step 2
Step 3
Configure your unique network access and risk policies. (30 minutes)
Step 4
Portnox’s cloud NAC solution prides itself on its partnerships and collaborations with industry-leading technologies to provide customers with the latest, greatest and most secure network access control solutions.
After completing the form, an email will be sent to you with the report download link.