
The Portnox Cloud delivers best-of-breed zero trust security capabilities to organizations of all shapes and sizes. Our platform provides complete visibility of all devices the minute they request access to the network or an application. When hackers get smart, we help you get smarter with always-on security essentials that prevent costly, sophisticated attacks, no matter how complex your IT environment.
Portnox arms organizations with the cloud and compliance infrastructure they need to embrace the benefits of digital transformation, while securing, controlling and appropriately managing access across the network.
Quick and easy deployment, low operational costs, and flexible device onboarding makes Portnox’s collaboration with cloud networking infrastructure an essential security tool for the innovative enterprise.
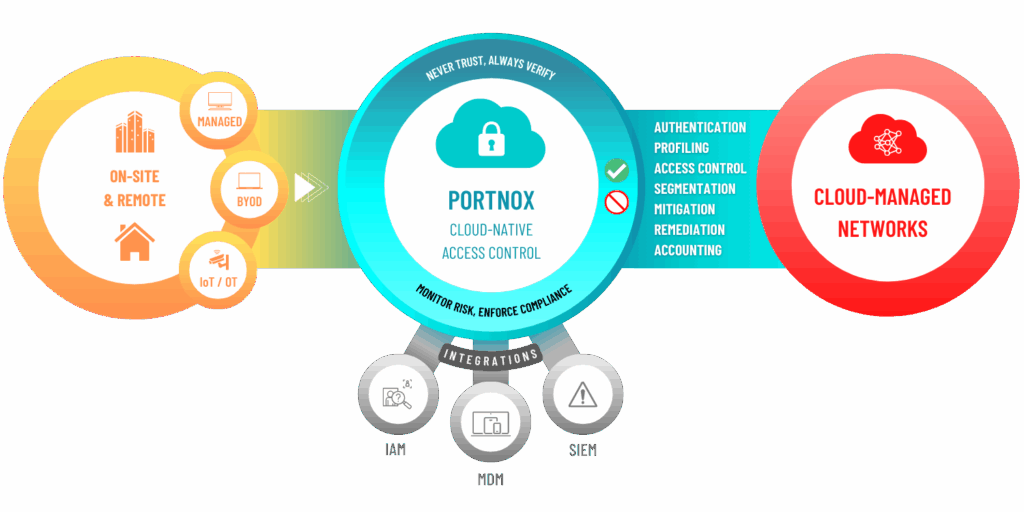
Portnox’s network access control platform delivers total awareness of all endpoints in use across the enterprise, and enforces 24/7 access control, risk mitigation, and compliance enforcement policies for networks and infrastructure – something no single platform can do from the cloud.
After completing the form, an email will be sent to you with the report download link.