The National Institute of Standards and Technology (NIST) sets guidelines and standards to ensure robust cybersecurity practices. The Portnox Cloud plays a pivotal role in achieving NIST compliance. By enforcing granular access policies, Portnox’s zero trust NAC ensures only authorized devices and users can access the network, mitigating risks of unauthorized access, data breaches, and insider threats. With continuous monitoring and real-time threat response capabilities, Portnox provides the necessary visibility and control to align with NIST’s rigorous security requirements.

NIST compliance requires the enforcement of access control policies to ensure that only authorized and authenticated devices and users are granted access to the network. Fortunately, the Portnox Cloud’s does just that – it’s key function is to deliver robust authentication, authorization, and accounting policies across wired, wireless and remote networks for managed devices, BYOD and IoT.
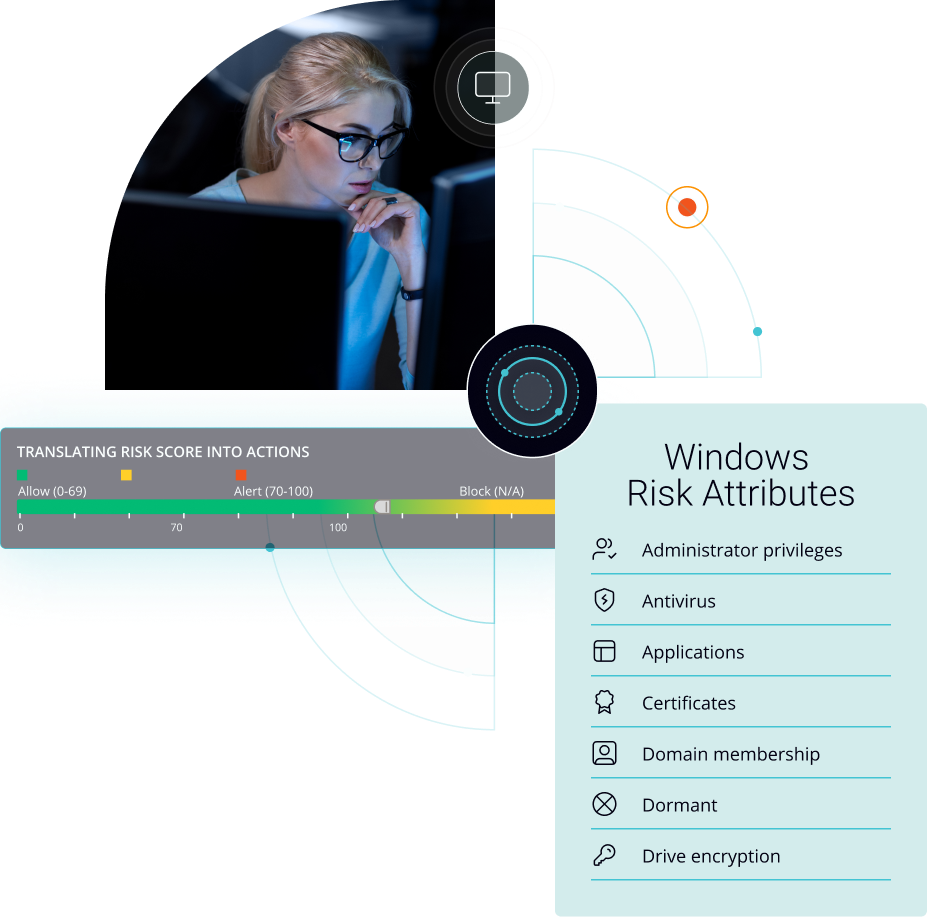
Portnox’s cloud-native NAC verifies the compliance of endpoints connecting to the network – a critical requirement within NIST security guidelines. Our zero trust platform assesses factors such as device health, presence of security patches, and updated antivirus software, ensuring that devices meet the necessary security standards before granting network access.
In line with NIST’s continuous monitoring requirements, Portnox can conduct device risk posture assessment 24/7, helping to identify any potential at-risk connected devices, and take action to quarantine and remediate endpoints that fall out of compliance. This functionality is enabled using the platform’s AgentP or by leveraging integrations with MDM solutions (Microsoft Intune and Jamf).
Portnox’s zero trust NAC allows organizations to define and enforce security policies aligned with NIST guidelines. These policies span authentication, access control, risk posture assessment, and endpoint remediation. The platform ensures that the defined policies are applied consistently across the network – no matter which access layers are in use (wired, wireless of remote).
The Portnox Cloud provides detailed visibility into network access requests, delivering records of endpoint location, device type, connected access layer, and more. This visibility allows organizations to generate reports and audits, demonstrating compliance with NIST standards. It also helps in identifying any potential compliance gaps or security risks that need to be addressed.
Portnox integrates with a wide variety of different Security Information and Event Management (SIEM) tools to enhance incident response capabilities. By sharing contextual information about network access and user activities, Portnox enables quicker and more accurate response to security incidents, aligning with NIST’s incident handling and response guidelines.
NIST is a broad, far-reaching set of regulations, and Portnox’s Access Control solutions have a robust set of features ready to meet these new challenges and help you achieve compliance. Fortify your network security with Portnox today!
NIST Compliance
The National Institute of Standards and Technology (NIST) provides several standards and guidelines for network security. One of the most prominent and widely used standards is the NIST Special Publication 800-53, titled “Security and Privacy Controls for Federal Information Systems and Organizations.”
NIST SP 800-53 establishes a comprehensive set of security controls that organizations, particularly federal agencies in the United States, can use to protect their information systems and networks. It covers various aspects of network security, including access control, identification and authentication, incident response, system and communications protection, and many others.
These controls are organized into families that address specific areas of network security. Some notable families include:
NIST SP 800-53 serves as a foundation for implementing effective network security measures, and it is frequently referenced and adopted by organizations beyond the scope of the federal government. It undergoes periodic updates and revisions to account for emerging threats and technological advancements in the field of network security.
NIST provides guidance on network access control through its Special Publication 800-53, which outlines security controls for federal information systems and organizations. Within this publication, several controls and recommendations are specified to enhance network access control. Here are some key aspects advised by NIST:
These recommendations are just a subset of the network access control guidance provided by NIST. For comprehensive and up-to-date details, it is recommended to refer to the NIST Special Publication 800-53 and other relevant publications issued by NIST.
Yes, NIST provides guidance on endpoint risk monitoring as part of its comprehensive approach to information security. While NIST Special Publication 800-53 focuses on security controls for federal information systems and organizations, NIST also offers other publications and resources that address endpoint risk monitoring specifically.
One such publication is the NIST Special Publication 800-137, titled “Information Security Continuous Monitoring (ISCM) for Federal Information Systems and Organizations.” This document provides guidance on establishing and implementing an effective continuous monitoring program, which includes monitoring the security of endpoints.
Within the context of continuous monitoring, NIST advises organizations to consider the following aspects related to endpoint risk monitoring:
While NIST publications provide valuable guidance, it’s important to note that organizations should adapt and tailor these recommendations to their specific needs and environments. Regularly referring to the NIST website and consulting the latest publications will ensure you have access to the most up-to-date guidance on endpoint risk monitoring and security.
Yes, NIST provides recommendations for endpoint remediation as part of its guidance on information security and risk management. While the specific recommendations may be found in various NIST publications, one of the key documents that addresses endpoint remediation is the NIST Special Publication 800-53, titled “Security and Privacy Controls for Federal Information Systems and Organizations.”
Within this publication, NIST outlines controls and best practices related to endpoint remediation. Here are some key recommendations:
These recommendations are not exhaustive, and organizations should consult the specific NIST publications and guidelines that provide detailed guidance on endpoint remediation, such as NIST Special Publication 800-53 and others related to vulnerability management and incident response. It’s important to adapt these recommendations to the organization’s specific requirements and environment.
After completing the form, an email will be sent to you with the report download link.