Extensible Authentication Protocol (EAP) is a key part of allowing wireless networks to use certificate-based authentication, so of course we love it. PEAP (Protected Extensible Authentication Protocol) takes it a step further, however, by encrypting the EAP requests in a secure tunnel for even greater security, and that’s the fastest way into our hearts.

Certificate-based authentication is not only easy to set up with Portnox (use us as your Certificate Authority or bring your own!), it’s also hands-down the best practice across the industry to keep your network secure. Never worry about another poorly-worded phishing e-mail designed to capture user accounts again with Portnox and certificate-based authentication!
Portnox supports SCEP (Simple Certificate Enrollment Protocol) so getting certificates deployed to all of your devices will be easy and fast. We seamlessly integrate with MDM solutions like Jamf and InTune too, so your mobile users aren’t left out. Your IT staff will love how easy it is to take your authentication methods to the next level, and your users will love not having to remember 10,000 passwords.

Staying ahead in IT means strengthening cybersecurity—and zero trust architectures now lead the charge. But let’s face it: embracing zero trust can feel daunting. With so many tools and complexities, it’s easy to lose your way.
To understand how organizations navigate zero trust, Portnox teamed up with TechTarget. We surveyed hundreds of IT and cybersecurity professionals across North America. Discover the insights we uncovered in our Trends in Zero Trust report.
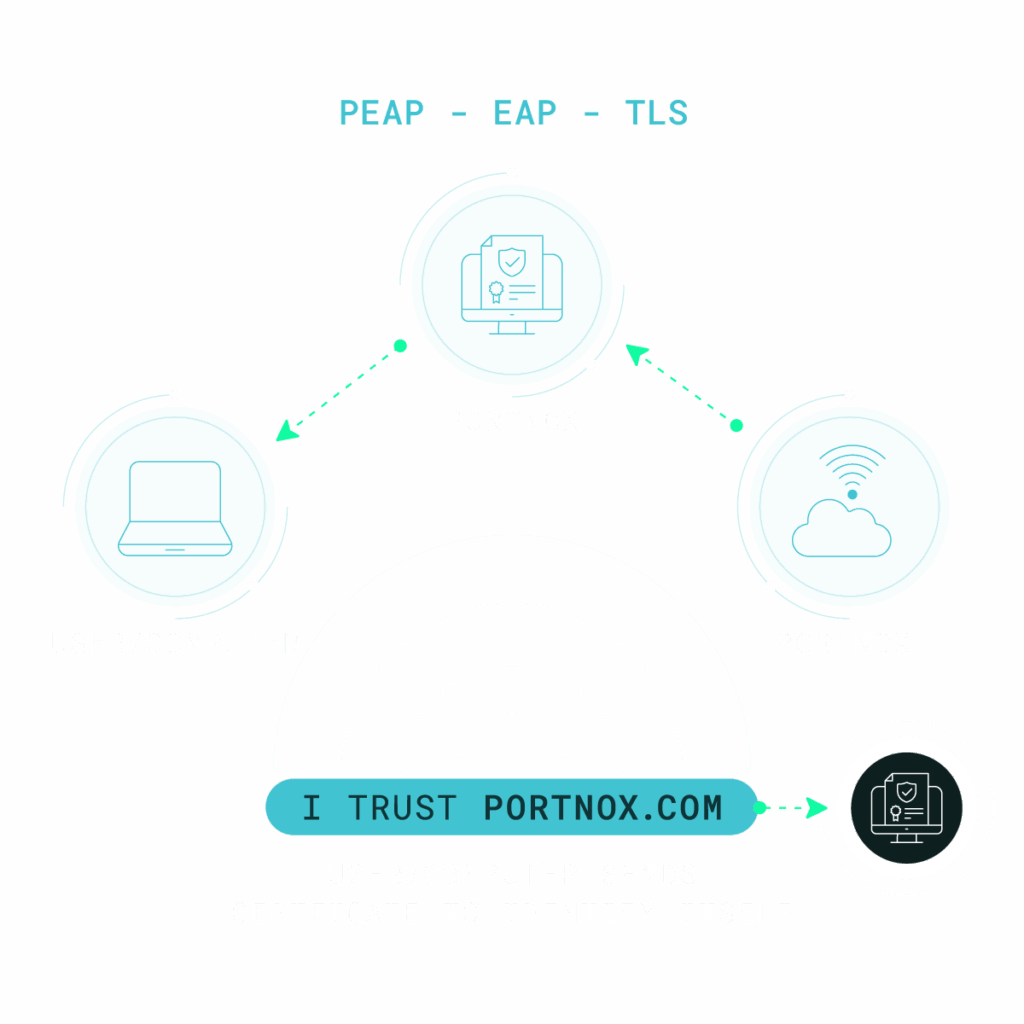
PEAP secures wireless authentication by creating an encrypted TLS tunnel between a client and a RADIUS server. Within this tunnel, credentials are safely exchanged using EAP methods, ensuring that only verified users and trusted devices connect to protected network environments.
PEAP authenticates Wi-Fi users in three steps: first, the client validates the server’s certificate; next, the user’s identity is verified using EAP credentials; and finally, encryption keys are exchanged to protect all data transmitted between the client and the server.
EAP is a flexible authentication framework supporting multiple credential types, while PEAP is a specific EAP method that adds TLS encryption for enhanced security. PEAP authenticates users through a secure server-based process, protecting credential exchange during wireless network access.
PEAP uses Transport Layer Security (TLS) encryption to protect communication between the client and the RADIUS server. TLS establishes an encrypted tunnel that secures credential exchange, ensuring authentication data remains confidential and tamper-resistant throughout the connection process.
Portnox Cloud natively supports PEAP authentication by validating user credentials and device posture before granting network access. When a device attempts to connect, Portnox uses PEAP to establish a secure, encrypted authentication tunnel back to the cloud platform. This enables robust protection for credential exchange while enforcing posture checks and policy decisions in real time.
Yes. Portnox Cloud extends PEAP authentication to both wired and wireless environments, ensuring consistent access control regardless of how devices connect. By integrating with existing network infrastructure and enforcing centralized policies from the cloud, Portnox provides secure PEAP-based authentication across access methods without requiring separate solutions for different connection types.
PEAP improves security by encrypting the authentication process and protecting credentials during transmission. Combined with Portnox Cloud’s policy engine, PEAP ensures that only authenticated users and compliant devices are granted access. This prevents credential theft and unauthorized connections that are common with open SSIDs or shared keys, strengthening the overall network access posture.
After completing the form, an email will be sent to you with the report download link.