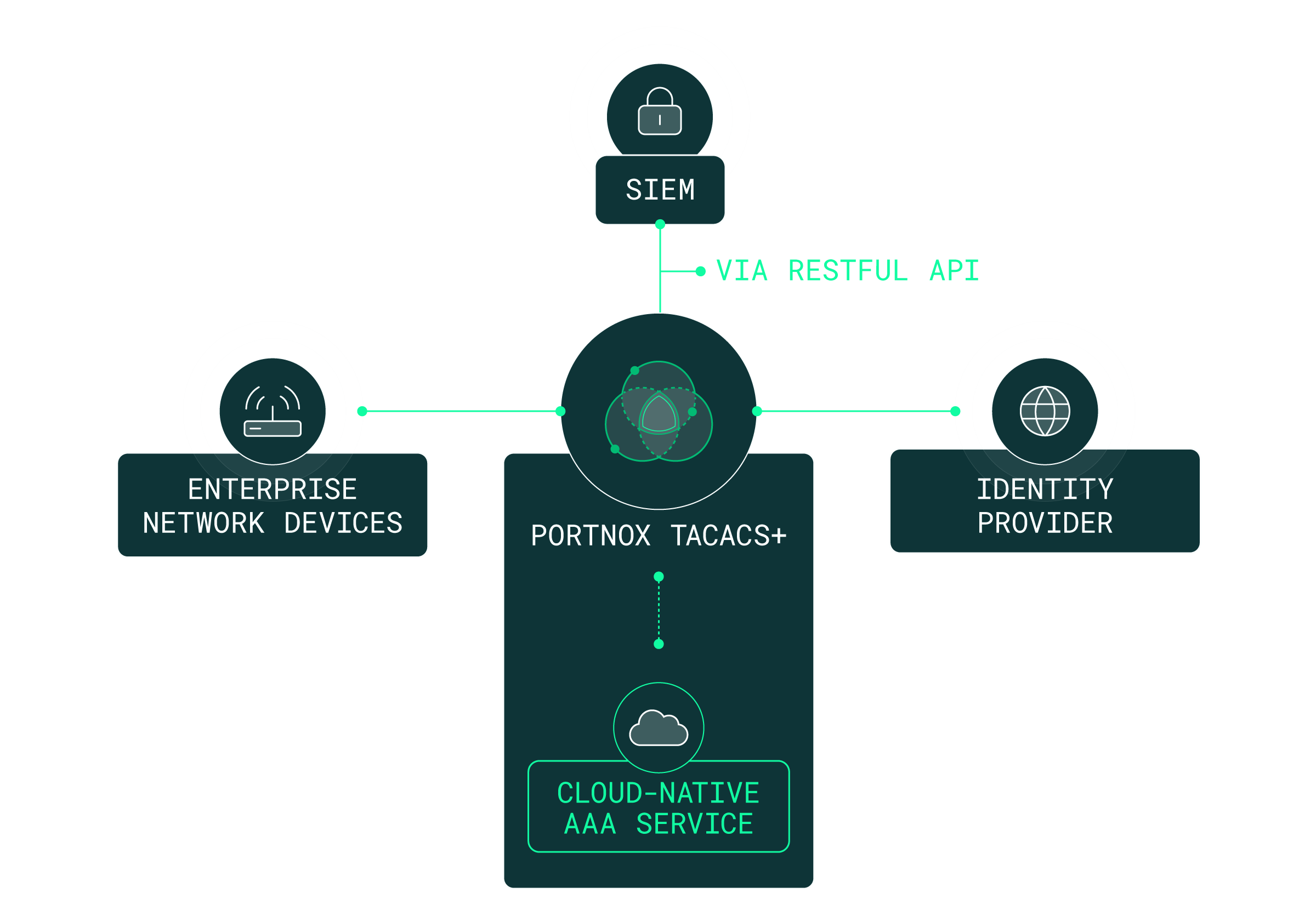
Even before the internet truly existed, managing infrastructure was complex – as shown by the fact that the TACACS (Terminal Access Controller Access-Control System) was first developed for ARPANET back in 1984. As networks have expanded, the need for a way to simplify device administration has only grown. Thankfully, Portnox’s cloud-native TACACS+ combines the features of TACACS+ with the ease of cloud-native software.
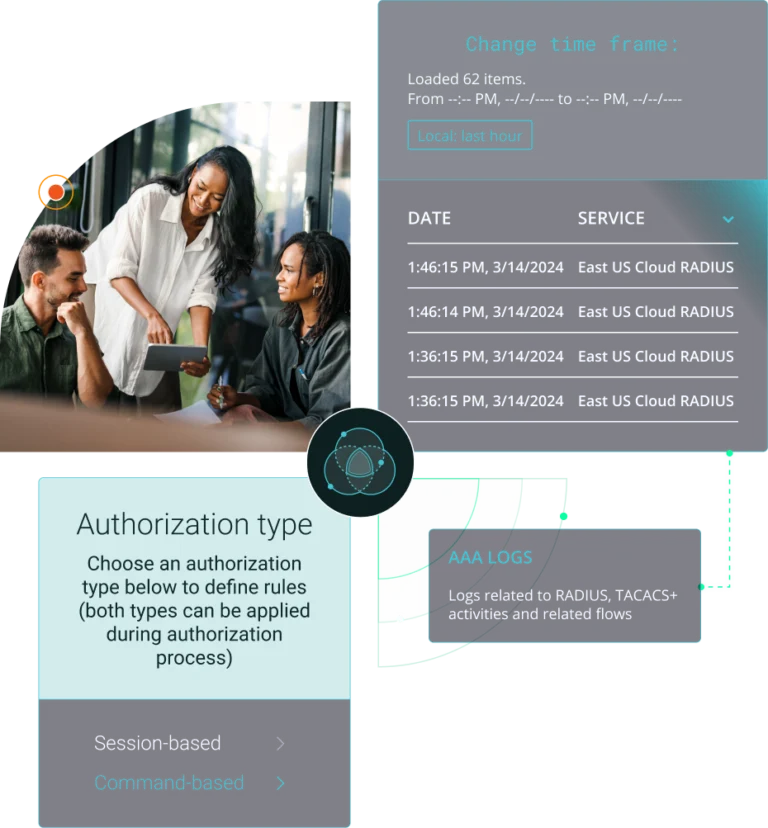
The strength of TACACS+ lies in AAA – Authentication, Authorization, and Accounting. With Portnox, you can control access down to the individual commands run on each device, AND have an audit trail in case you need to figure out who did what when.

Staying ahead in IT means strengthening cybersecurity—and zero trust architectures now lead the charge. But let’s face it: embracing zero trust can feel daunting. With so many tools and complexities, it’s easy to lose your way.
To understand how organizations navigate zero trust, Portnox teamed up with TechTarget. We surveyed hundreds of IT and cybersecurity professionals across North America. Discover the insights we uncovered in our Trends in Zero Trust report.
TACACS is a network protocol used for remote authentication and access control. It communicates with an authentication server to verify user credentials, determine access privileges, and centralize network device management across routers, switches, and firewalls.
TACACS+ is an enhanced version of TACACS that separates authentication, authorization, and accounting (AAA) functions. It encrypts all communication between network devices and the TACACS+ server, providing centralized control over device access and administrative actions.
TACACS+ authenticates users by verifying credentials through a central server before granting device access. Administrators can define granular policies to control commands, device groups, and privileges while maintaining detailed logs for each session to improve accountability and network visibility.
TACACS+ encrypts entire packets using symmetric key algorithms such as AES. A pre-shared key authenticates communication between the device and server, protecting usernames, passwords, and authorization data from interception throughout the authentication process.
RADIUS authenticates users for network access, while TACACS+ manages administrative access to devices. TACACS+ offers full-packet encryption, granular command control, and uses TCP. RADIUS, used by Portnox Cloud, is open-standard, lightweight, and ideal for scalable user authentication.
Yes. Portnox Cloud’s TACACS+ integrates with identity providers and IAM systems like Microsoft Entra ID and Okta. This allows organizations to centralize user identities and enforce consistent access policies across network device administration. By tying TACACS+ to your IAM platform, you gain better control over privileges and reduce administrative overhead associated with managing separate credential stores.
Portnox Cloud’s cloud-native architecture allows TACACS+ to scale across multi-site and global environments without additional on-prem infrastructure. Policies and role definitions are centrally managed and consistently enforced everywhere. This makes it easy for large enterprises to support thousands of administrators and devices while maintaining strong access controls and auditability as they grow.
After completing the form, an email will be sent to you with the report download link.