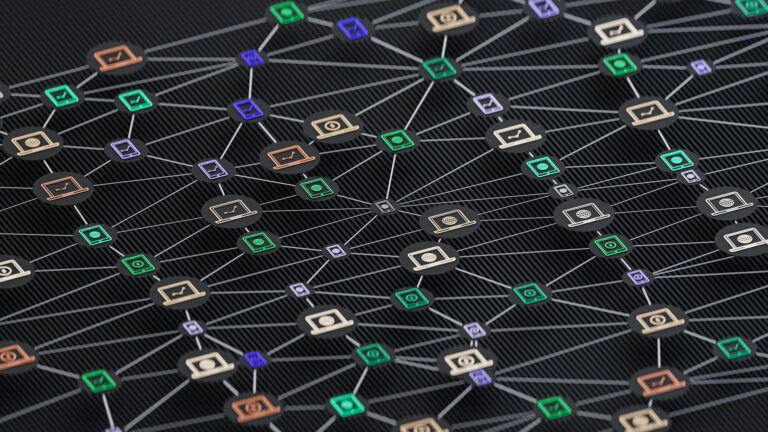
Getting control over who’s accessing your network is no longer just a security precaution. It’s a daily need for businesses that want to keep mistakes, breaches, and hidden risks to a minimum. You can bolt on fancy tools or invest heavily in firewalls, but without a solid access control structure, it’s like locking the front door and leaving the windows wide open. Network access control solutions help fix that by making sure only trusted users and devices get through and stay inside your system safely.
As more devices connect and more employees sign in from everywhere, a hands-off or old-school system just won’t cut it. That’s when solid network access rules become more than just helpful—they’re necessary. When done well, access control improves visibility and limits weak spots across your digital environment. But implementing it the right way is what really makes the difference.
Why Network Access Control Solutions Matter
Imagine running an office where anyone can show up, grab a desk, and plug into your network with no questions asked. That’s what it’s like without network access controls—open access, unknown devices, and a whole lot of risk. The goal of network access control solutions is simple: give the right people access, keep everyone else out, and track what’s connecting at all times.
Without proper controls in place, businesses often face:
– Unchecked access by personal or unknown devices
– Increased exposure to unsafe connections or outdated software
– Lack of visibility into real-time user activity
– Trouble meeting security standards or audits
The good news is, putting controls in place doesn’t have to be complicated. It comes down to creating clear access guidelines and enforcing them consistently. When you manage connections with purpose, you avoid surprises and reduce the chance of human error.
Some benefits of having a solid access structure include:
– Preventing unauthorized users from getting to sensitive data
– Spotting problems before they grow into serious security issues
– Allowing bring-your-own-device (BYOD) setups without added risk
– Applying rules consistently across remote and in-office teams
One real-life example is a mid-sized company that switched to remote operations. Before access controls were added, they had no visibility into how personal devices were connecting to critical platforms. After implementing a solution and verifying devices by default, they saw a sharp drop in unauthorized access and tech support issues.
Understanding what’s in your network, creating smart rules, and using a system that closes coverage gaps keeps your environment safer and easier to oversee—even during growth or shifts in operations.
Key Features of Effective Network Access Control Solutions
Picking a network access control solution isn’t about checking off a few feature boxes. It’s about finding tools that are the right fit for your setup, team needs, and future plans. Whether you’re building from scratch or replacing something outdated, the right features can shore up weak points and smooth operations.
Here are key features to look for:
1. User and device authentication
Your system should verify every person and device before access is granted. This includes checking passwords, device security levels, certificates, and compliance with internal rules.
2. Real-time monitoring
It’s important to know who is connected and when. The right solution alerts you if an unknown device logs in or if someone tries to go beyond their allowed permissions.
3. Role-based access control
Not everyone should see everything. By creating access levels by role or department, you limit the fallout from a misstep or breach.
4. Policy enforcement
Let the system check whether users have antivirus updates, encrypted devices, or meet other requirements before letting them in.
5. Integration with your existing tools
Your solution should work with your identity platforms, device managers, and reporting systems without extra volume or process drag.
These features solve problems, but they’re most valuable when paired correctly. Real-time alerts don’t help if your team can’t act right away. Authentication is only reliable when paired with proper device health checks and a logical permission structure.
If your IT staff is working with fewer hands, look for automation and clear reporting to take away repetitive monitoring tasks. That helps your team prioritize what really needs their attention instead of chasing down odd login issues or unanswered error logs. It’s much better to prevent confusion caused by outdated rules and undefined roles up front instead of scrambling after an incident.
Steps to Successfully Implement Network Access Control Solutions
Getting started takes a little planning. Effective network access control solutions need more than just installation. It helps to know your setup, list your users, and have an idea of where tools are being logged into and from. That foundation helps guide the process and keeps things efficient.
Here’s a basic process that makes rollout easier and faster:
1. Assess your environment
List users, devices, and the software they access. Understand where people are coming from and what tools they use most often.
2. Define access policies
Draw hard lines around who can reach what. Think through staff roles and device reliability when building those rules.
3. Test before you deploy company-wide
Start with a specific team or department so you can work out kinks, handle weird use cases, and improve the overall flow.
4. Automate wherever it makes sense
Set up automatic alerts and actions if someone breaks a rule. Let your solution handle routine enforcement so your team isn’t drowning in tickets.
5. Train your team
Explain what the access controls do and why they matter. Make instructions brief and easy to follow—most employees don’t want to click through a 20-page guide.
6. Revisit and revise often
Business changes fast. Your policy might need tightening or loosening depending on new apps, remote users, or device updates.
Picture a team working both from home and in-office. Without strict access rules, someone using a personal laptop with no malware protection might get through. That’s a big risk. But with enforced policies, even that laptop must meet baseline standards first. Over time, this keeps things clean and helps your IT staff avoid playing catch-up.
Common Pitfalls and How to Avoid Them
Even good plans fall short when the rollout doesn’t match the organization’s daily routine. When systems trip up regular work, users get frustrated, and security gets bypassed. Many of these issues come from the same few missteps.
Avoid problems by watching out for these:
– Skipping the planning stage
Jumping into setup without thinking through your needs often leads to mismatched features or a system that’s too hard to manage.
– Setting vague policies
If your access rules are unclear, your system won’t enforce them properly. Be specific and practical when defining who gets what.
– Overloading the IT team
If only one or two people can fix problems when they come up, there’s going to be a bottleneck. Automate checks and give managers limited tools to help.
– Leaving out personal or mobile devices
Even if most devices are company-issued, users will try to connect phones and tablets. Ignoring those endpoints leaves gaps in your system.
– Letting the system get stale
Just because something worked last year doesn’t mean it works now. Devices age out and employees change roles, so the structure can’t sit untouched forever.
When alerts stack up, or employees can’t get into their tools, dig in and fix the friction right away. If five users are locked out right after a policy update, that might be a clue that the rules changed too fast or weren’t documented well. Stay on top of small problems so they don’t escalate into bigger breakdowns.
Keeping Your Network Protected with Ongoing Attention
Strong network access control isn’t a set-it-and-forget-it project. As teams change and workflows evolve, your policy will need updates to stay strong and effective. Something that made sense when your operations were centralized might not work as well now that users shift between locations or schedules.
Make time once a quarter to check policies, user lists, and connection logs. Watch for patterns and permissions that aren’t being used. That way, you’re proactively tightening things up before any damage is done. A few small changes now beat cleaning up a big breach later.
Listen to user feedback too. Are staff confused by login paths? Organized check-ins can uncover things that metrics won’t. Sometimes the fix is as simple as closing out old accounts or updating access groups to reflect new projects.
This isn’t just about tech. It’s about teamwork. When department leads have input into access rules, they’ll point out what’s really needed—or what hasn’t been used in months. That back-and-forth makes your policies more effective and easier to manage for the long haul.
Access control works best when it grows with you and reflects how your team actually works. Reliable processes, strong systems, and regular reviews make sure your network stays protected no matter the changes ahead.
Improve your system’s defenses with our expertise in creating tailored solutions for your business. Discover how Portnox can help enhance your company’s network access control solutions. From initial assessment to policy updates, our approach ensures your network stays secure and efficient. Reach out today to explore how we can support your cybersecurity needs.