Remote Access Security: A New Reality
No matter what industry you’re in, your company has likely been affected by the coronavirus outbreak. In fact, you’re probably reading this from home as we speak. Remote work is a new reality. While many of us will return to the office when it’s deemed safe, many companies have seen first-hand the value and ability of employees to work from home and will look to enhance and expand their remote workforces when things return to normal.
For network security teams, this poses a host of new challenges, particularly given the loss of physical control over those newly at-home corporate devices. But have no fear…we’re here to share the important and often overlooked remote access security best practices to consider as you elevate your remote access visibility and security.
I. A Bridge Too Far
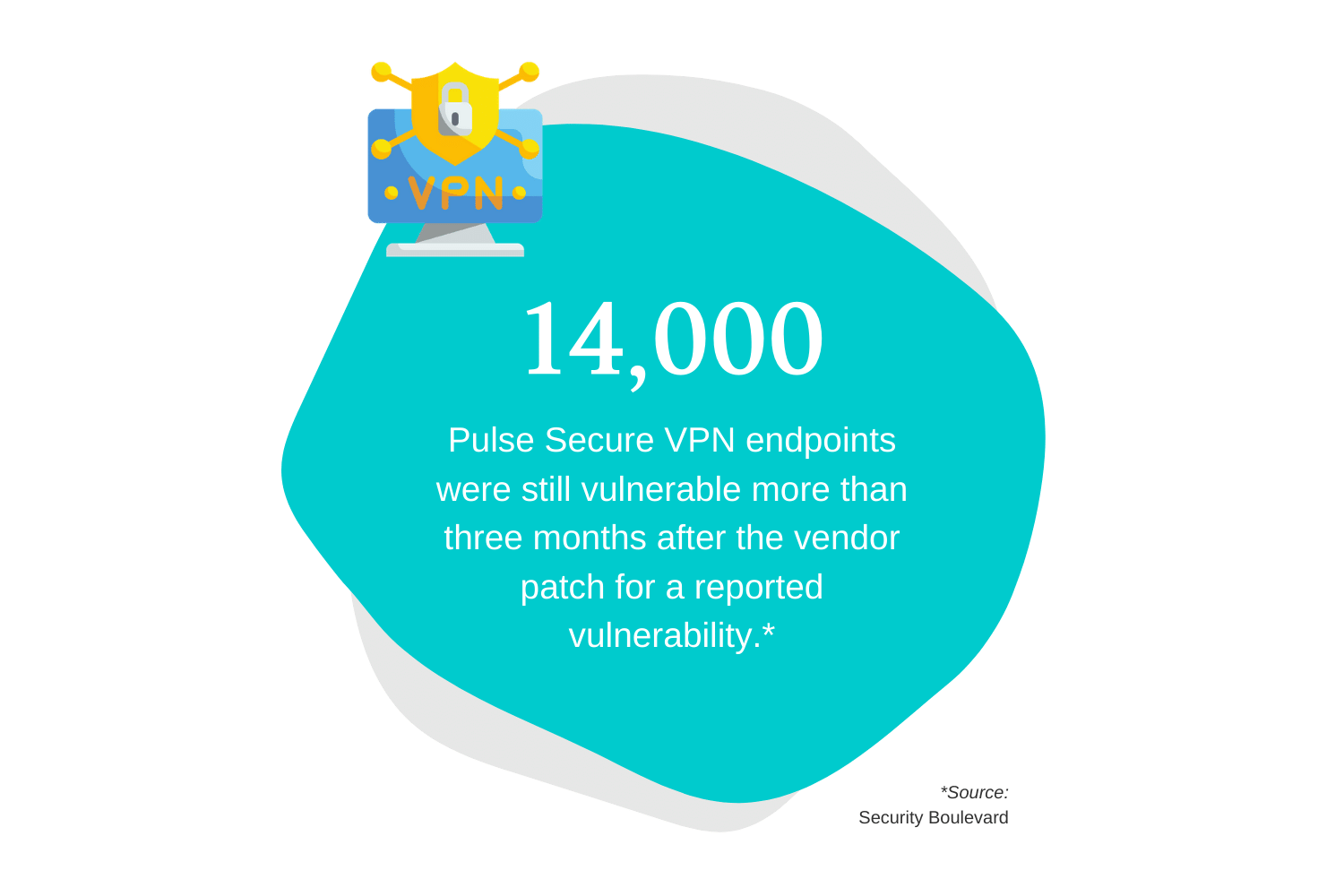
No,we’re not talking about the 1977 WWII film starring Michael Caine and Sean Connery (albeit a great movie). Today, companies use VPN gateways and/or virtual remote desktops to provide their remote employees with access to the corporate network and other internal resources.
The problem, however, is that some of the most popular VPN vendors have admitted to significant vulnerabilities that would allow any person from the internet with no credentials to use the VPN gateway as the bridge to your corporate network and crown jewels.
II. Are You Afraid of the Dark?
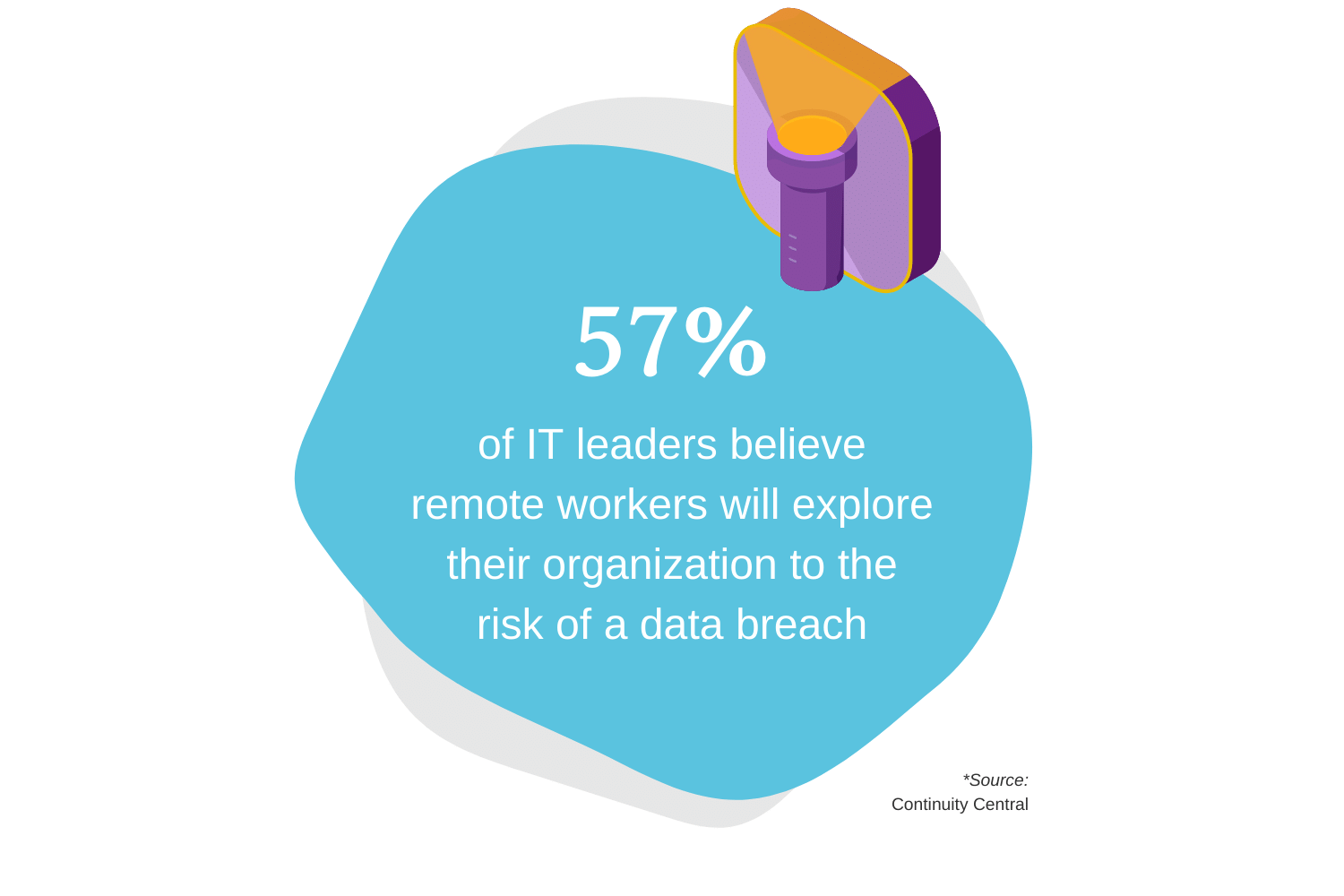
90s kids will get this Nickelodeon reference, although it’s not the show we’re focused on today. We’re all afraid of the dark, and rightly so…scary stuff happens in the dark. That’s why you need to be continuously aware of the risk posture of every remote device connecting to the network continuously – all the time, every time, no matter location or device type. This will allow you to react in real-time to potential threats before $#!% really hits the fan.
Want to unlock the next three remote access security best practices? Download the full eBook today!
