Legacy NAC meant bulky hardware, complex maintenance, and endless patches. Portnox NAC brings you a different experience: a SaaS solution purpose-built for today’s hybrid and distributed networks. You get real-time device visibility, risk-based access controls, and automated compliance enforcement — all delivered from the cloud.
No more MFA fatigue. No more forgotten passwords.
Credentials are the weakest link no matter how strong your security posture. Implement passwordless authentication with digital certificates and never worry about a phishing attempt to steal passwords ever again.
Portnox can be your certificate authority or integrate with a 3rd party. We also support SCEP (Simple Certificate Enrollment Protocol) so deploying certificates to all your devices will be simple.
Gain real-time visibility of endpoints trying to connect to your network and infrastructure, plus additional context such as their location, device type, and requested access layer for authentication.
Extend zero trust security coverage to company devices, BYOD and IoT / OT alike, no matter if they’re authenticating via wired ports, WiFi or VPN.
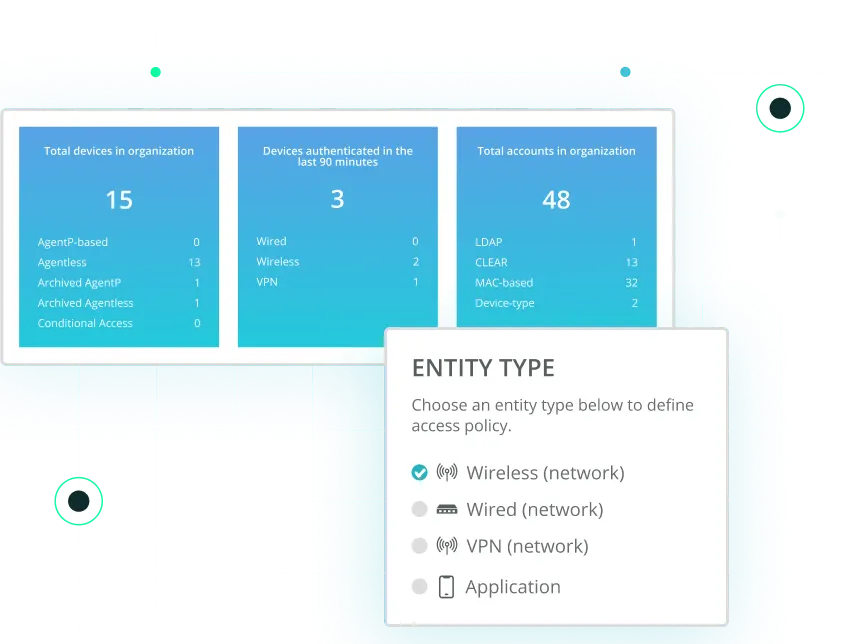
Define and enforce unique access control policies based on roles, locations, device types and more across your various network access layers.
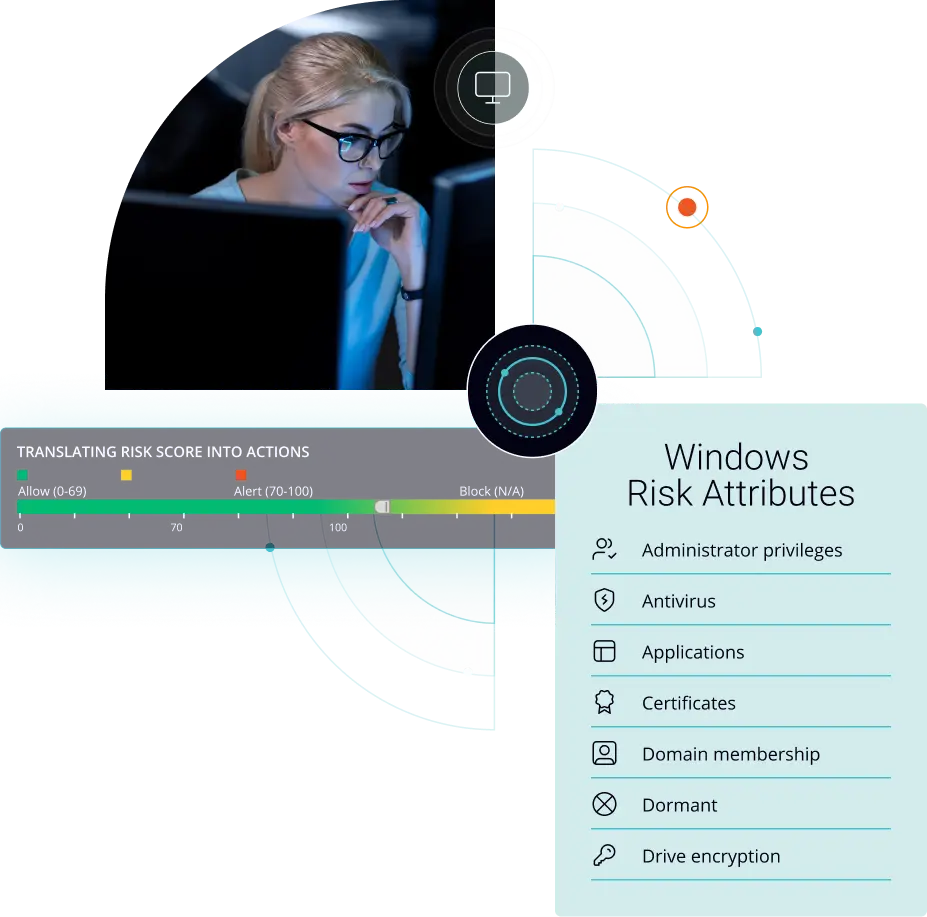
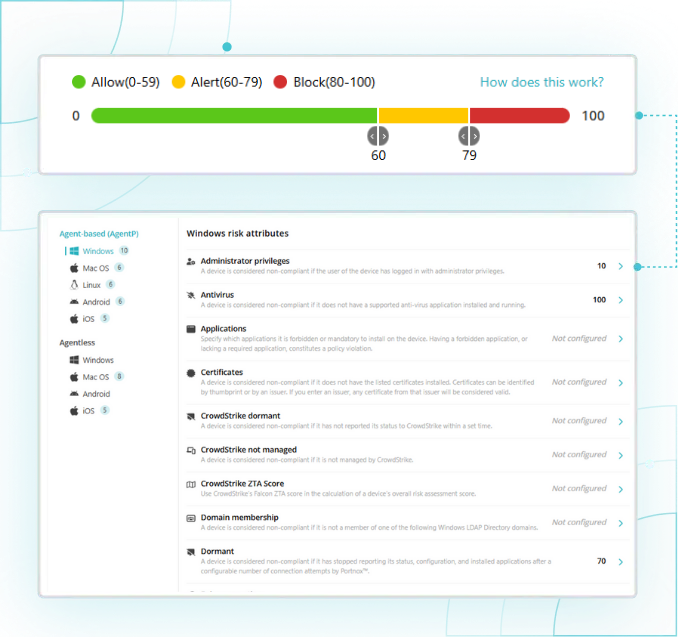
Additionally, leverage Portnox Cloud’s powerful risk assessment policy configuration capabilities to continually monitor the risk posture of connected devices – including managed and BYOD – enabling your network administrators to understand the true zero trust security posture of the network at any point in time.
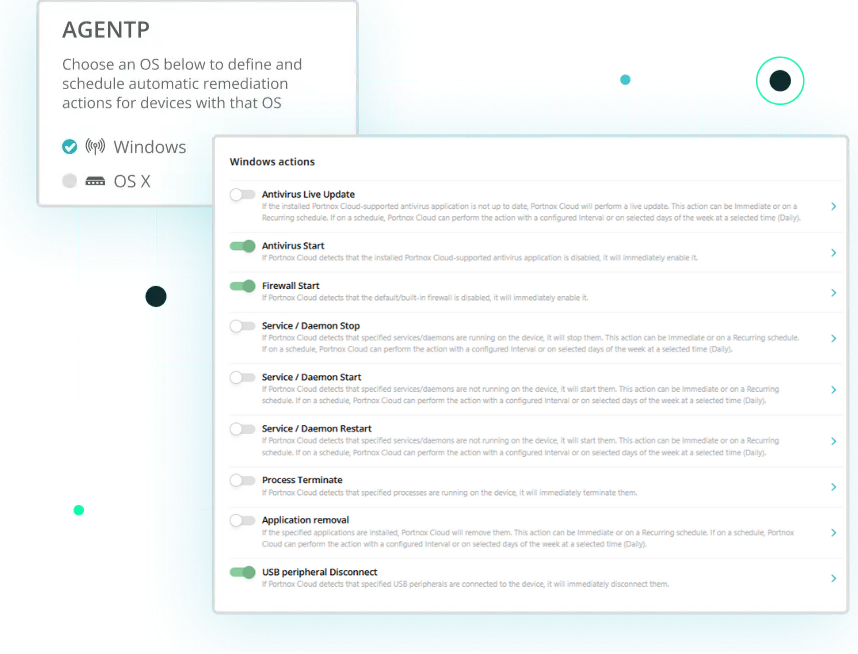
Quarantine vulnerable, non-compliant devices and return them to a healthy, compliant state automatically by setting unique endpoint remediation policies in accordance with your compliance requirements.
Portnox Cloud’s compliance enforcement capabilities can help your organization adhere to industry-specific regulatory and compliance standards such as HIPAA, GLBA, PCI DSS, GDPR and beyond.
Mindbendingly easy setup
Connect with a Portnox expert for a tailored demo of Portnox NAC.
Configure your network devices to authenticate through Portnox Cloud RADIUS.
Configure your unique network access and risk policies.
Complete testing and fully deploy across your entire network.
See how easy it is to create a risk policy with Portnox Cloud!
If you’re exploring Portnox NAC, extend your zero trust strategy further with Portnox ZTNA and TACACS+.
Together, they unify network, application, and infrastructure access control in one cloud platform for stronger security and simpler operations.
Cloud-native, posture-aware access delivering secure, passwordless connectivity to SaaS and private apps without VPN complexity.
Cloud-delivered administrative access control providing centralized authentication, authorization, and command auditing for all network infrastructure.
“
”
“
”
“
”
“
”
Request a Portnox demo today and discover the many capabilities of our cloud-native zero trust access control and security platform.
After completing the form, an email will be sent to you with the report download link.