With the new NIS 2 regulations, the E.U. makes a giant leap forward in creating a consistent, comprehensive cybersecurity framework to protect critical assets across all its members. NIS 2 introduces new requirements for protective measures, increases the scope of covered industries,, creates reporting obligations, and introduces financial penalties for entities that do not meet the new standards. Explore how Portnox can help you avoid fines and meet these stringent new regulations.

NAC ensures that only authenticated and authorized devices can access network resources, aligning with NIS2’s emphasis on access control and identity management. This prevents unauthorized access and mitigates the risk of malicious activities within the network. Portnox employs 802.1x access control, the gold standard for many years due to its broad adoption and iron-clad encryption.
NAC systems enforce organizational security policies across all devices attempting to access the network. Portnox can ensure compliance with security standards, such as ensuring that devices are properly patched, have the latest antivirus updates, and adhere to secure configuration settings, thus supporting the NIS2 requirement for entities to take appropriate technical measures to manage security risks.
NAC limits the movement of potential threats across the network. This segmentation helps protect sensitive information and critical infrastructure, which is a core aspect of the NIS2 Directive. Portnox will help you segment your network based on role, department, or any way your organization needs to limit lateral movement and make sure you’re compliant with least-privileged access.
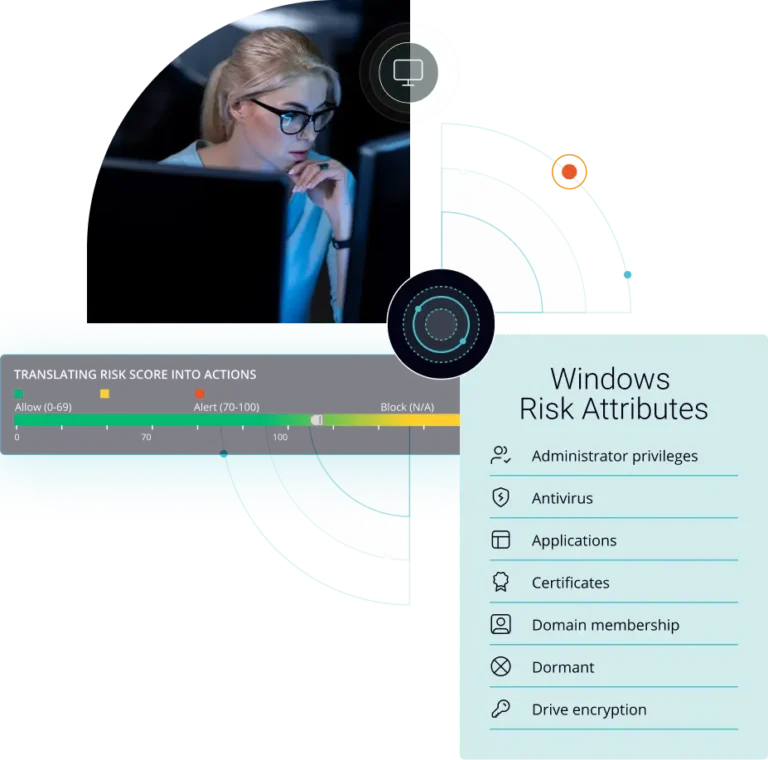
NAC solutions offer continuous monitoring of network activities, enabling the detection of unusual access patterns or behaviors that may indicate a security threat. This capability supports the NIS2’s directive on early threat detection and effective response to incidents. Portnox has a robust risk policy engine that will let you define security policies for devices and applications that contain your most critical data and provide you with options beyond just deny/allow/quarantine. Things like updating anti-virus can be done automatically without user or IT intervention to make sure devices are not putting you at risk.
NAC can automate responses to detected security threats, such as isolating a compromised device from the network to prevent the spread of malware. This automated incident response is in line with NIS2’s requirement for entities to have measures in place to prevent and minimize the impact of security incidents. IoT devices are particularly vulnerable to compromise, which is why Portnox introduced our IoT Device Trust feature. Not only can we fingerprint those devices that may be hiding on your network, with Secure MAB we can alert you if your security camera suddenly starts acting like a laptop and automatically removes it from the network.
NAC systems generate detailed logs and reports on network access, user activities, policy enforcement, and security incidents. These reports provide essential documentation for compliance audits, helping organizations demonstrate their adherence to the NIS2 Directive’s requirements for security measures and incident reporting. Portnox’s robust alerting and reporting will let you stay on top of who is trying to access your network, along with critical information like what type of device and where they are coming from. Our customizable dashboards will let you keep important information visible.
NIS2 is a broad, far-reaching set of regulations, and Portnox’s Access Control solutions have a robust set of features ready to meet these new challenges and help you achieve compliance. Fortify your network security with Portnox today!
NIS 2 compliance
After completing the form, an email will be sent to you with the report download link.