Enron. WorldCom. Adelphia. Tyco. Qwest. Of all the things that marked the early years after the turn of the century, the wave of corporate fraud scandals has left a lasting mark on the landscape of American business. In the wake of these scandals, the ground-breaking Sarbanes-Oxley act was passed, and SOX Compliance became priority number one for private and public companies alike. Portnox helps you comply with SOX security standards so you can avoid your own scandal.
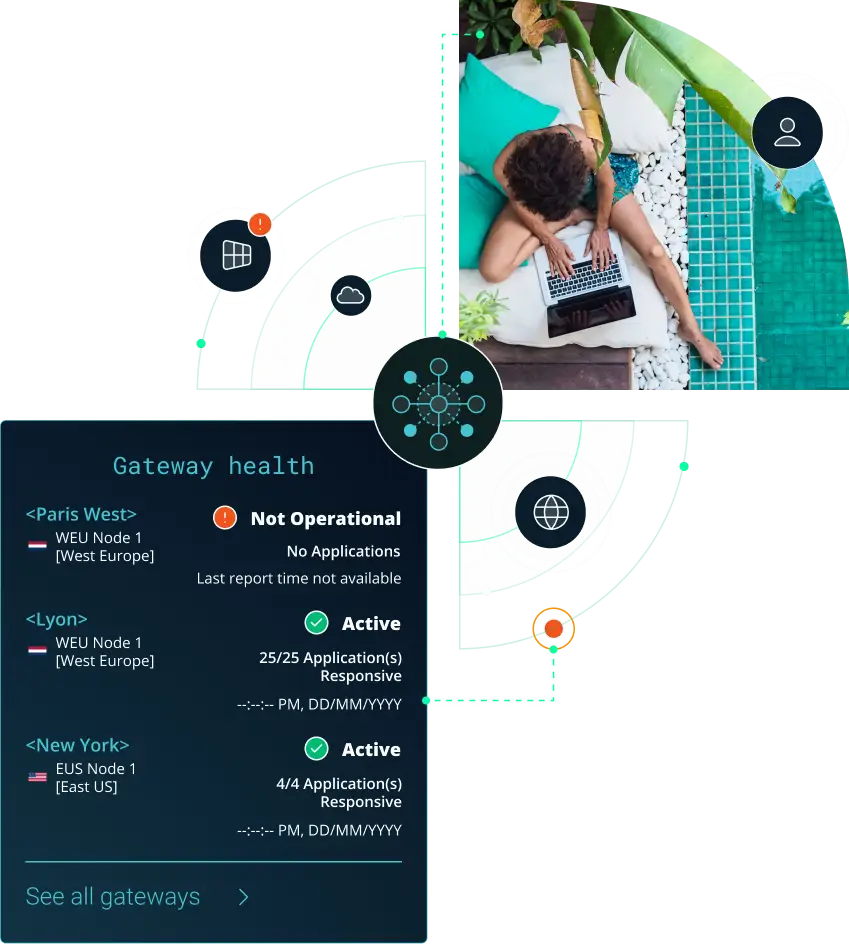
Network access control is designed to provide user accountability by logging and monitoring network access activities. This helps in meeting the SOX requirement of maintaining accurate and reliable records of financial transactions and system access. Portnox offers a built-in cloud RADIUS server, which delivers the gold standard protocol for authentication, authorization and accounting (AAA) services, so you have a record of all access activities.
NAC can contribute to data protection efforts by enforcing policies that restrict access to sensitive data based on the adherence to security policies by connected devices. The Portnox Cloud has a robust risk policy engine that allows you to enforce requirements like up-to-date anti-virus and OS versions. Portnox also features automated remediation options, so user devices can be brought into compliance without the need for your IT team to intervene.
Portnox provides comprehensive auditing and reporting capabilities, which can aid in compliance auditing required by SOX. These reports can demonstrate the implementation and effectiveness of access controls, user accountability, and data protection measures. Additionally, Portnox TACACS+ allows you to easily comply with SOX change management requirements with robust accounting for networking infrastructure.
SOX emphasizes the segregation of duties to prevent fraud and errors. The Portnox Cloud can assist in enforcing segregation of duties by implementing role-based network access, which allows access to resources based on a user’s role and responsibilities. This ensures that confidential resources such as financial data are available only to those whose job function requires them.
NAC can enhance incident response capabilities by detecting and responding to unauthorized or suspicious network activities. IoT devices are a particularly attractive target for a data breach, and Portnox’s IoT Device Trust not only identifies any shadow IoT devices but can also do behavior analysis so if a camera begins acting like a laptop your IT team can take immediate action.
SOX Compliance
SOX compliance refers to meeting the requirements of the Sarbanes-Oxley Act, a U.S. law designed to improve corporate governance and ensure the accuracy and integrity of financial reporting. While SOX is focused on financial controls, it relies heavily on IT security controls that protect systems and data involved in reporting. Portnox Cloud supports SOX compliance by strengthening access control and accountability.
Access control is critical for SOX compliance because it helps prevent unauthorized access to financial systems, reporting tools, and sensitive data. Portnox Cloud enforces identity-based access policies and device posture checks before granting connectivity. This helps ensure only authorized users and trusted endpoints can access systems tied to financial reporting, reducing the risk of tampering or improper access.
Yes. Portnox Cloud supports SOX audit readiness by providing centralized logging of authentication attempts, access decisions, and policy enforcement actions. These records help demonstrate that access controls are consistently applied and monitored. With clear visibility into who accessed what and when, organizations can simplify audit preparation and strengthen accountability for systems related to financial reporting.
SOX compliance is not a one-time checklist—it requires ongoing oversight of internal controls, including IT access controls. Portnox Cloud helps maintain continuous enforcement through real-time device visibility and automated policy actions when endpoints become risky or non-compliant. This reduces operational gaps and helps ensure access control remains consistent as users, devices, and environments change.
After completing the form, an email will be sent to you with the report download link.