Portnox ZTNA provides secure remote access from any location with cloud-native zero trust controls. Get fast, passwordless, risk-based authentication for every SaaS and on-prem application your business relies on.

The last thing your IT team needs is a constant barrage of tickets asking “Why is everything suddenly so slow?!” Yet, other ZTNA solutions provide security at the expense of your network performance.
Portnox ZTNA was designed to provide zero trust application access that is fast, secure, scalable—and did we mention fast? Modernize your remote access without sacrificing productivity.
Let’s face it—passwords are insecure, and MFA is annoying. Both end users and IT teams face issues caused by lax password security measures, leaving systems vulnerable to bad actors who use brute force, phishing, and man-in-the-middle attacks to gain unauthorized access.
Unify your zero trust access control with passwordless authentication across your entire organization, from your network to your apps to your remote connections, and more.
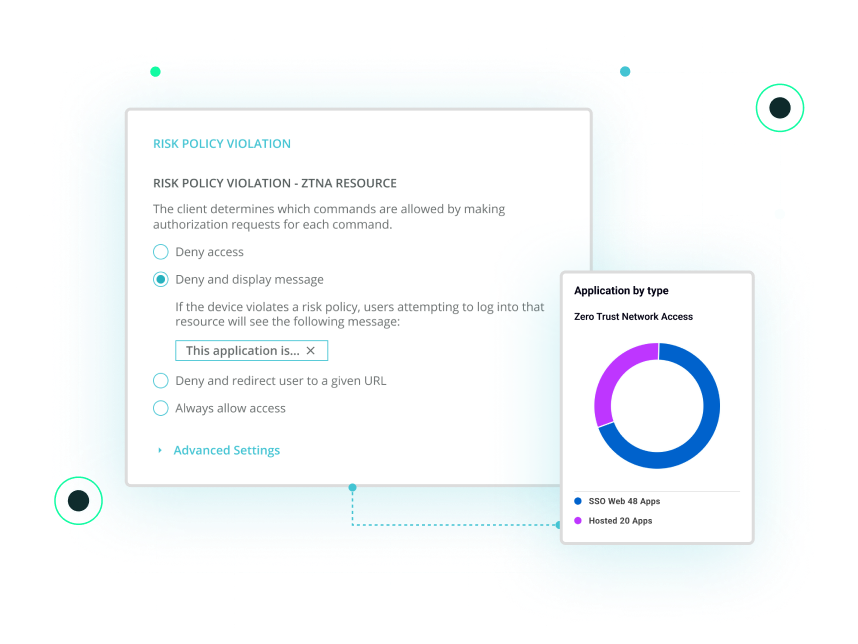
Passwordless authentication is crucial to protecting your assets, but once someone is in, what are they allowed to access? Don’t just give away keys to the castle—segment your network to increase zero trust application access. Implement smart access control policies based on roles, location, and more.
Go a step further with least-privileged access. Make sure people only have access to the resources they need to do their job, protecting you from lateral movements by internal and external threats.
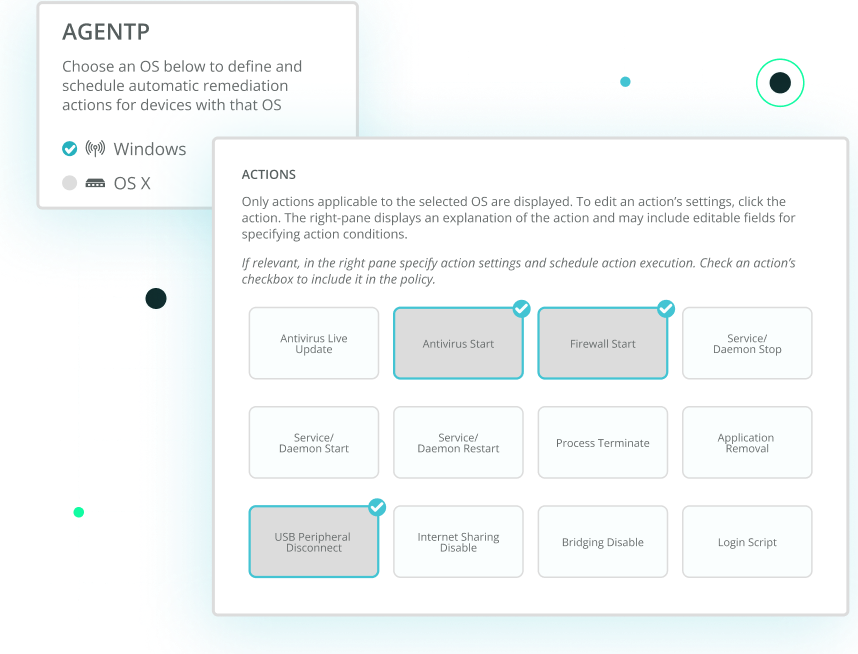
The success of your entire cybersecurity approach hinges on your ability to control risk. Portnox provides you with the ability to identify devices that pose a threat to your environment. Create policies for any device, make sure antivirus is up to date, check for forbidden software, ensure firewalls are running, and much more. Our robust policy engine will help you mitigate risk, freeing up your IT team for more business-critical tasks.
Discover how the New Albany Floyd County Consolidated School District secured its network and scaled access control in record time with Portnox Cloud. Facing a diverse mix of 15,000 endpoints and limited IT resources, the district deployed Portnox Cloud across 20 buildings in weeks — not months — with real-time device visibility, seamless Chromebook integration, and no new hardware. The result: stronger security posture, simplified operations, and broad device coverage from day one.
Secure remote access
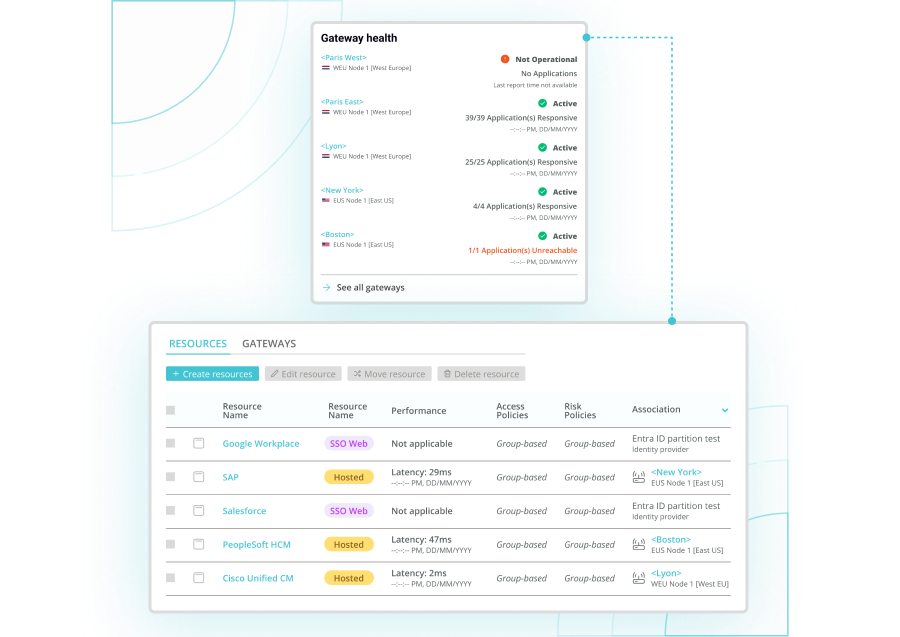
Secure remote access with Portnox ZTNA allows users to securely access private applications without exposing the network. Portnox uses a zero trust model that verifies user identity, device posture, and risk context before granting application-level access. This approach eliminates implicit trust and ensures users only connect to the resources they’re explicitly authorized to use.
Portnox ZTNA replaces traditional VPNs by providing secure remote access at the application level rather than the network level. Instead of placing users “on the network,” Portnox brokers connections to specific applications based on identity and device compliance. This prevents lateral movement, reduces attack surface, and simplifies access for remote and hybrid users.
Portnox secure remote access supports both agentless and lightweight agent-based deployment models. Users can access applications securely through a standard web browser without installing software, while optional agents enable deeper device posture checks. This flexibility allows organizations to balance security, user experience, and operational requirements without sacrificing zero trust principles.
Portnox enforces secure remote access using zero trust policies that continuously evaluate user identity, device posture, and contextual risk. Access is granted only after policies are met and can be revoked in real time if conditions change. Every access request is verified explicitly, ensuring no user or device is trusted by default—even after authentication.
Yes, Portnox secure remote access integrates natively with Microsoft Entra ID for identity-based access decisions. This allows organizations to extend Entra ID policies to private applications, enforce conditional access, and apply device compliance checks. The integration enables consistent identity governance across cloud, SaaS, and private applications without adding complexity.
Portnox secure remote access reduces credential-based attacks by validating more than just usernames and passwords. Access decisions are based on identity, device posture, and risk signals. Even if credentials are compromised, attackers are blocked if the device is unmanaged, non-compliant, or fails policy checks—preventing unauthorized access and lateral movement.
Portnox secure remote access is purpose-built for hybrid and remote workforces. It enables employees, contractors, and third parties to securely access applications from anywhere without VPNs. By enforcing consistent zero trust policies across users, devices, and locations, Portnox ensures secure access while maintaining a frictionless user experience
You’ve started your zero trust journey—now bring it together with Portnox Cloud.
Move beyond point solutions to a single, cloud-native access control platform built for modern enterprises. Eliminate blind spots, reduce complexity, and enforce smarter security across every user, device, and application.
Cloud-native, posture-aware access delivering secure, passwordless connectivity to SaaS and private apps without VPN complexity.
Modern, cloud-based NAC securing wired and wireless access with instant device discovery, posture validation, and automated enforcement.
After completing the form, an email will be sent to you with the report download link.