Welcome to the future of IoT! Imagine this futuristic scenario…
An electric and autonomous Taxi or Uber car pulls up at a charging station on the side of the road. In order to receive the charge, the car is required to communicate and pay the station, while the station “needs” to “trust” that indeed it will be paid for the electricity before it starts charging. The two machines need to communicate and transact with each other. In this future, how will authentication, authorization and trust between Internet connected machines be established? One could think of a machine having a “credit history” and a “trust score” of some sort, based on past performance that is auto-communicated between these IoT machines.
The “trust score” could be affected by a few things. If a machine’s computer hasn’t been updated with the latest security patches, firewall and malware protection, other machines won’t process transactions with it. Or if its processor or other parts have a sketchy supply chain record that are not trusted that would lower the score. Perhaps having skipped a payment somewhere could lower the score as well. In these cases, the charge station would most likely not provide the electricity for the charge. Or, in a worse scenario, if this autonomous uber car has been compromised as far as security, and is allowed to perform the transaction – there could be potential challenges starting with the service station not being paid, all the way to attacks where viruses and malware are being spread and even leading the way to DDoS attacks, such as the Dyn Attack on October 21, 2016 that affected large sections in Eastern USA and Europe.
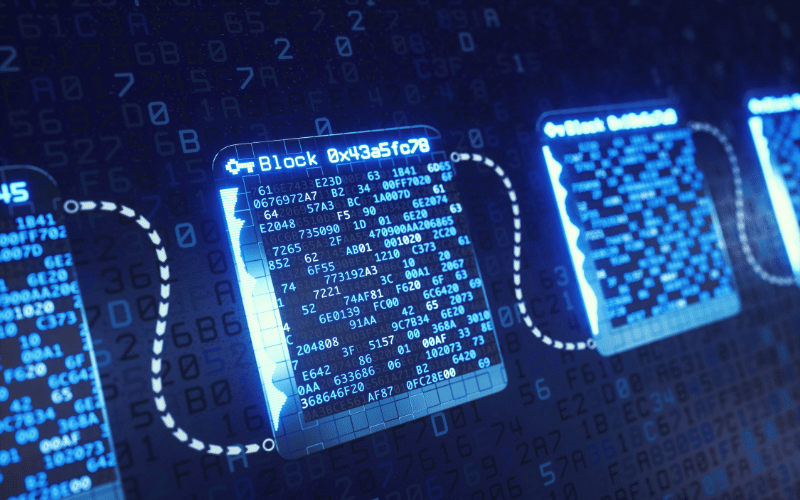
Introducing the Blockchain of Things
IoT includes all hardware devices that are connected to the Internet. We have seen tremendous growth in the IoT sector in the last few years. Gartner research estimates that there will be roughly 20.4 billion IoT connected devices by the year 2020. That’s around the corner. An influx of smart devices could pose both security and reliability issues, particularly with devices that thus far have not been connected to the network. In the last year or so there has been more talk about using Blockchain technology to secure IoT devices and machines, and there is even a school of thought called Blockchain of Things emphasizing this potential solution.
Blockchain is considered to be one of the most promising technologies for the future. It is essentially a decentralized distributed ledger (a data base or record book), that provides a way to record and transfer data in a way that is transparent, safe, auditable, and resistant to outages. The data is stored on computers and business servers around the world, and in the future it could be used to record many different types of data. Currently the main use-case for Blockchain is in the realm of cryptocurrency. The technology was first rolled out in January 2009 as the underlying tech for Bitcoin and has since been used for other cryptocurrencies such as Ethereum.
On the blockchain system, all computers/ end-nodes confirm that a transaction took place and is therefore an authorized occurrence, confirming that everything about the transaction is legitimate before giving the transaction an approval. Every copy of the record must match up for all end-nodes. It is as if we are all standing around watching the electric autonomous Uber or Taxi pull up to that electricity charging station and connect with the charging station’s communications, all agreeing that the money went from the car owner to the charge station, as well as other data such as the car came to this specific geo-location and that the correct amount was logged.
Blockchain Technology & Network Security
With each day going by, it is becoming clear that blockchain technology could play a role in achieving increased security, reliability and trust in IoT networks. We believe that these scenarios are going to be part of our normal routine within the next 5-10 years. A routine control of risk will be as important as ever when machines are performing the transactions and communications amongst themselves, without us humans, (although they will be communicating in essence on our behalf) and outstanding trust protocols will have to be set in place so that this future can work seamlessly and securely.