
Over the last decade, the internet of things (IoT) has matured as a discipline, and today represents a variety of defined use cases that deliver proven efficiency and productivity benefits across a plethora of industries. IoT remarkably improves process automation, supply chain management and adherence to regulatory compliance to significantly bring down capital expenditures and operational costs.
Additionally, IoT represents a major driver of digital transformation within today’s enterprises, with the potential increase margins, boost profit, and improve the overall employee experience.
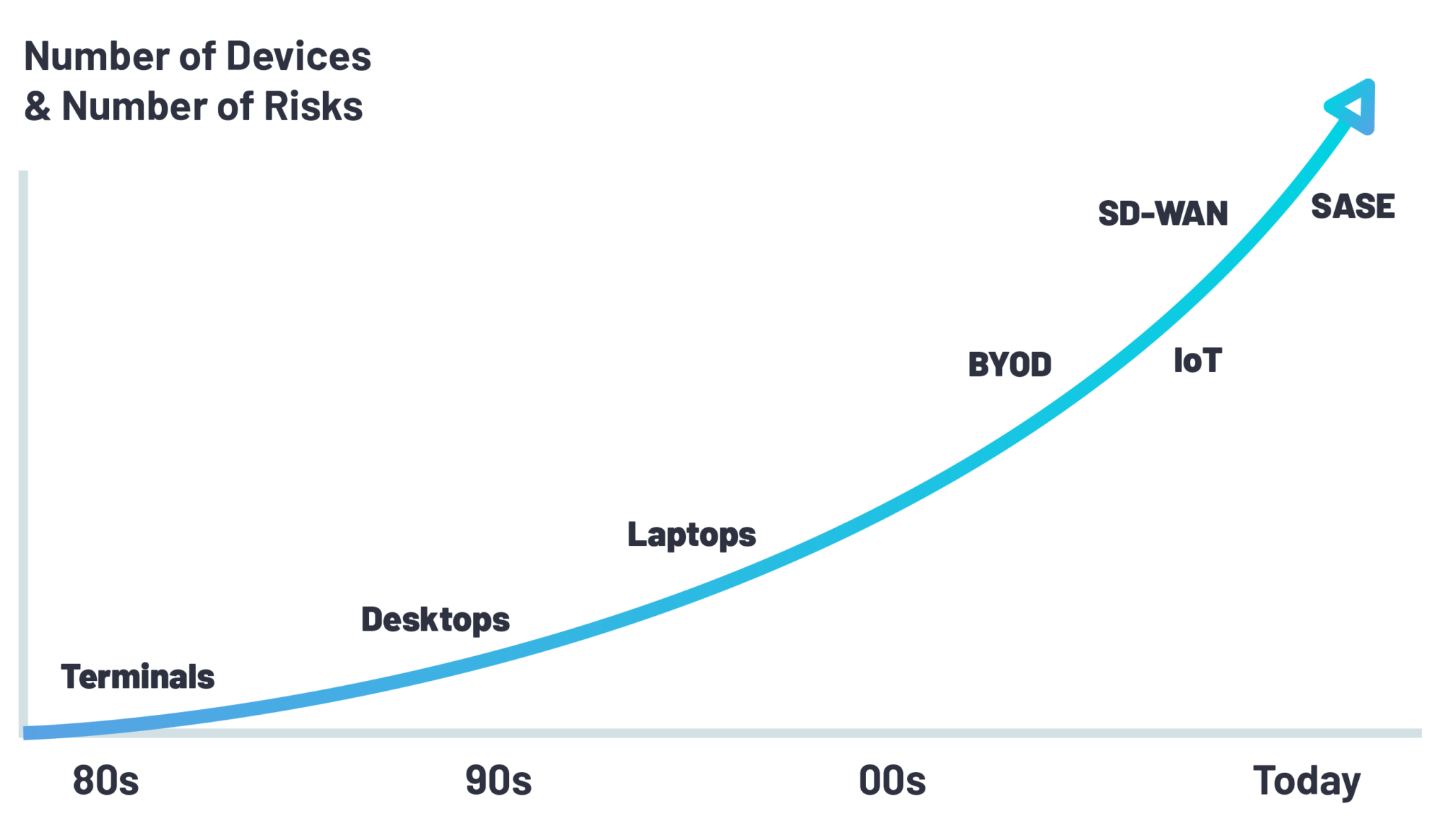
Like the adoption of BYOD policies, the rise of IoT integration into business operations is creating a new landscape of cybersecurity vulnerabilities. Traditionally, IT security teams have focused their attention on securing standard employee devices like desktops and laptops. Over the last ten years, minimal investment has gone into the development of employee skills with regard to IoT security. Today, organizations struggle with one fundamental function: discovering IoT devices on their networks.
Because of their inherent “newness,” the security risks connected to IoT devices are less understood. Unfortunately, this means that securing them is often not done adequately. Why? Well, there are two main reasons:

Today, controlling access within an IoT environment remains the largest security challenge that companies face when connecting devices. This primarily includes controlling network access for the connected IoT devices themselves. This challenge derives from a subset of difficulties, including identity management, system availability, data integrity and more.
To mitigate and eliminate cybersecurity risks brought on by new IoT endpoints, organizations are turning to network access control solutions for added visibility, understanding, and control over IoT devices. In a sense, this is a replication of the same approach taken for traditional managed and BYOD endpoints in use locally and remotely.
As we’ve discussed, there is a huge variety of IoT devices and a general lack of centralized management with regards to IoT security. Many IoT devices still rely on IT security technology from the 1980s, with no password brute force controls and no available patches.
Furthermore, legacy NAC solutions like Cisco’s Identity Services Engine (ISE) and HP Aruba ClearPass haven’t evolved to address the full swath of modern IoT security challenges. In many respects, they struggle to scale for IoT, are hampered by complex 802.1X implementations, and are even vulnerable to MAC spoofing.
Today, it’s a matter of ensuring IoT devices can be properly identified, authenticated, monitored and controlled so that they’re unable to compromise the network. Network security engineers thus need a NAC solutions that support current IoT security needs, such as threat awareness, containment, and mitigation.
Through its network access control solutions, Portnox provides complete visibility, control and management of IoT devices connected or connecting to enterprise networks. Gaining knowledge and control capabilities for IoT devices security is essential for minimizing exposure to digital business risks arising from IoT security vulnerabilities, and understanding IoT security issues provides an accurate posture assessment of network health.
Portnox CLEAR enables organizations to discover, control and manage IoT devices connecting both on and off premise, and effectively control access based on a device’s level of risk, according to pre-defined network security policies. Plus, you can eliminate geo-redundancies with cloud-based 802.1X authentication for all devices.
Gain access to all of Portnox’s powerful zero trust access control free capabilities for 30 days!
After completing the form, an email will be sent to you with the report download link.