Whether you’re a fan of digital transformation or not, there’s no denying that the shift to the cloud is engulfing enterprise IT. According to Gartner, over the next five years, over $1 trillion in compounded IT spending will be directly or indirectly impacted by the cloud shift, making cloud computing one of the most disruptive forces of IT spending since the early days of the digital age.
That said, it’s time to debunk some of the most common myths regarding cloud security before an outdated IT stack exposes your organization to emerging digital business risks.
Check out our Top 5 mythbusters Infographic here!
Myth #1 – The Cloud Isn’t Secure
The top concern among C-Suites and IT teams alike is that cloud-based security solutions are more prone to external threats than legacy security solutions.
Debunked: On-premise security appliances require firmware upgrades to protect against known exploits, resulting in a constant need to keep the solutions up-to-date. In addition, configuration changes could expose the network to potential vulnerabilities, requiring tedious maintenance of management procedures and periodic penetration testing. However, cloud-based security solutions are constructed, from the outset, to evolve to address relevant threats in the current cyber security landscape. David Linthicum, a leading cloud analyst and VP at Cloud Technology Partners, explains that the security of the cloud is on par with the security of any external device: “Anything that can be possibly accessed from the outside – whether enterprise or cloud – has equal chances of being attacked, because attacks are opportunistic in nature”.
Myth #2 – The Cloud Is Still Too ‘New’ To Be Trusted
Cloud-based applications and services are relatively new on the IT front. So why trust them?
Debunked: An increasing number of both large and small to medium-sized enterprises across a variety of industries – government, healthcare, ecommerce etc. – are employing cloud-based solutions for everything from human resource management to network security. According to IDG Research, “Cloud technology is becoming a staple to organization’s infrastructure as 70% have at least one application in the cloud”.
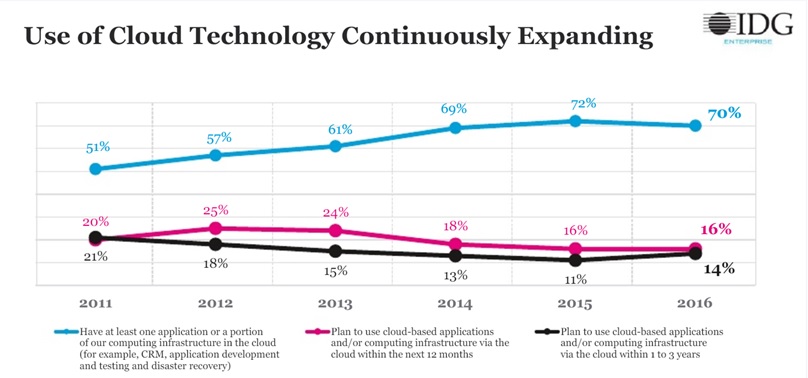
Reference: “2016 IDG Enterprise Cloud Computing Survey”
Myth #3 – The Cloud Is Great for Productivity Apps, But Not for Securing the Network
There is big difference between cloud productivity apps, and performing key security actions, such as Network Access Control (NAC) from the cloud.
Debunked: NAC is a growing concern for CIO/CISOs and IT teams in large to SMEs due to the increased need to gain control over digital business risks. And the stigma of the cloud being less secure isn’t necessarily correct. Gartner reports that by 2018, the 60% of enterprises that implement appropriate cloud visibility and control tools will experience one-third fewer security failures.
Myth #4 – Cloud Solutions Require Re-Educating IT Teams
Training IT teams to deploy a cloud-based security-as-a-service solution would require significant time and resources.
Debunked: Cloud solutions inherently cut time and costs associated with security management in IT teams, freeing them up to carry out more productive and profitable action items. That’s added to the easy and instant deployment associated with cloud-based solutions including automatic system updates, usage demos, access to use cases, and more.
Read our Debunking Cloud Security Myths White Paper for more fun facts!
Myth #5 – Cloud Solutions Can’t Help with Compliance
Cloud solutions are constantly changing – one minute they are a “must have” security tool, and the next they are an imminent source of risk to company information. How can you trust cloud security solutions uphold compliance?
Debunked: Cloud solutions are taking heed and are doing their part to relieve this part of the “IT headache”. Many solutions integrate compliance standards into their product while allowing for modifications to the network policy where necessary. Built-in compliance is a winning strategy for business success, and ensures that there aren’t any loopholes the IT team is missing out on.
As Gartner puts it, “By 2020, a corporate ‘no-cloud’ policy will be as rare as a ‘no-Internet’ policy is today”. While in many cases, hype can have dangerous potential, in the case of cloud security, it’s a win-win situation: a win for digital transformation and a win for the IT team that’s eager to expand their business value proposition.
Portnox CLEAR – Security-as-a-Service Solution: The first completely cloud-based Security-as-a-Service solution for Network Access Control (NAC), CLEAR controls access for all devices and users to wired, wireless and virtual networks, to effectively confront digital business risks and cybersecurity threats.
