802.1X authentication is the industry standard for controlling who and what can access a network. As a foundational control within modern Network Access Control (NAC), 802.1X authentication ensures users and devices are verified before they gain access to wired or wireless infrastructure.
Portnox delivers cloud-native 802.1X authentication that removes hardware dependencies, simplifies deployment, and strengthens identity-based network access. Built for zero trust environments, Portnox helps organizations apply strong authentication across users, endpoints, and IoT devices in distributed networks.

As organizations support remote work, BYOD, and IoT at scale, enforcing authentication at the network edge is critical. 802.1X authentication has remained the gold standard because it provides a proven, standards-based way to control access at the port and access point level.
802.1X authentication enables organizations to:
802.1X authentication is built around three core components:
When a device attempts to connect, the authenticator blocks traffic until the authentication process is completed. Using the Extensible Authentication Protocol (EAP), credentials or certificates are securely exchanged and validated. Network access is then granted based on defined authentication policies such as role, device type, or security context.
This model enables consistent authentication across wired and wireless networks without exposing infrastructure to unauthenticated devices.


Traditional 802.1X authentication deployments often rely on on-prem authentication servers, complex certificate workflows, and appliance-based infrastructure. Platforms such as Cisco ISE and Aruba ClearPass can provide strong authentication controls but typically introduce long deployment cycles and ongoing operational overhead.
Portnox removes this complexity with a cloud-native 802.1X authentication architecture:
This approach delivers enterprise-grade authentication without the cost and complexity of legacy NAC platforms.
Portnox enables organizations to apply 802.1X authentication across common enterprise scenarios:
By combining 802.1X authentication with cloud-native NAC, organizations gain visibility and control across every connected device.


Zero trust security requires strong authentication before access is granted. 802.1X authentication enforces this principle at the network layer by ensuring that no user or device is trusted by default.
Portnox extends 802.1X authentication with zero trust-aligned capabilities such as certificate-based identity, contextual policies, and continuous enforcement. This ensures network access decisions are driven by authentication and policy rather than network location.
Deploy secure 802.1X authentication without hardware, manual certificate workflows, or unnecessary operational overhead.
Start your free 30-day trial or request a demo to see how Portnox simplifies 802.1X authentication for modern, zero trust networks.
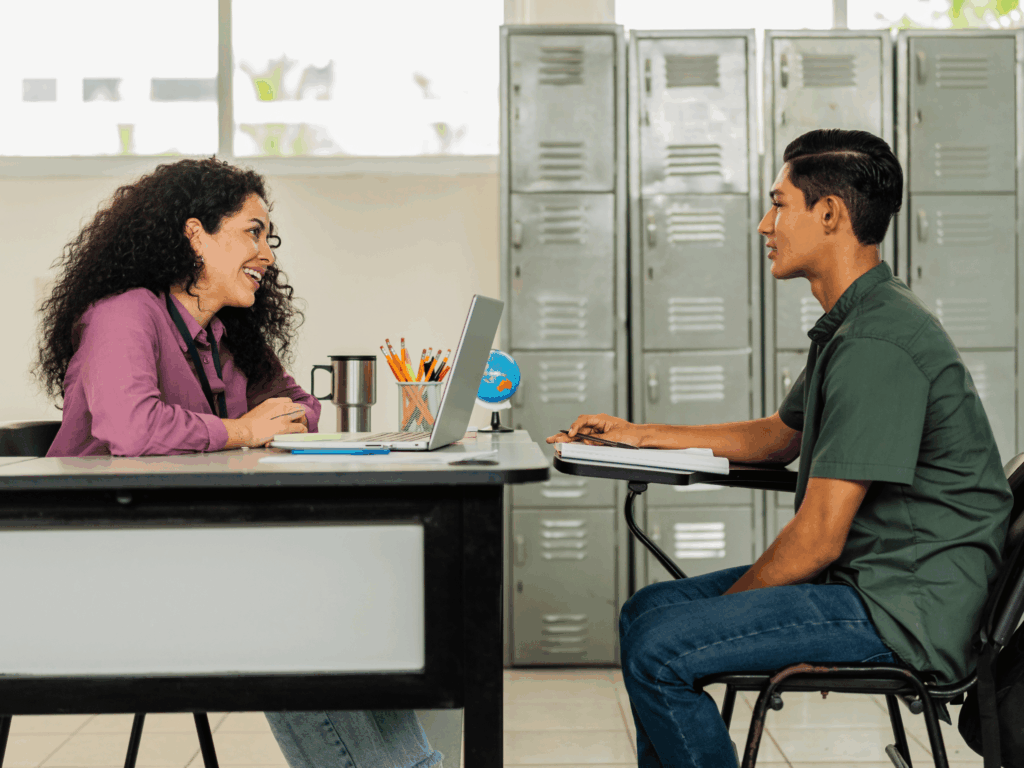
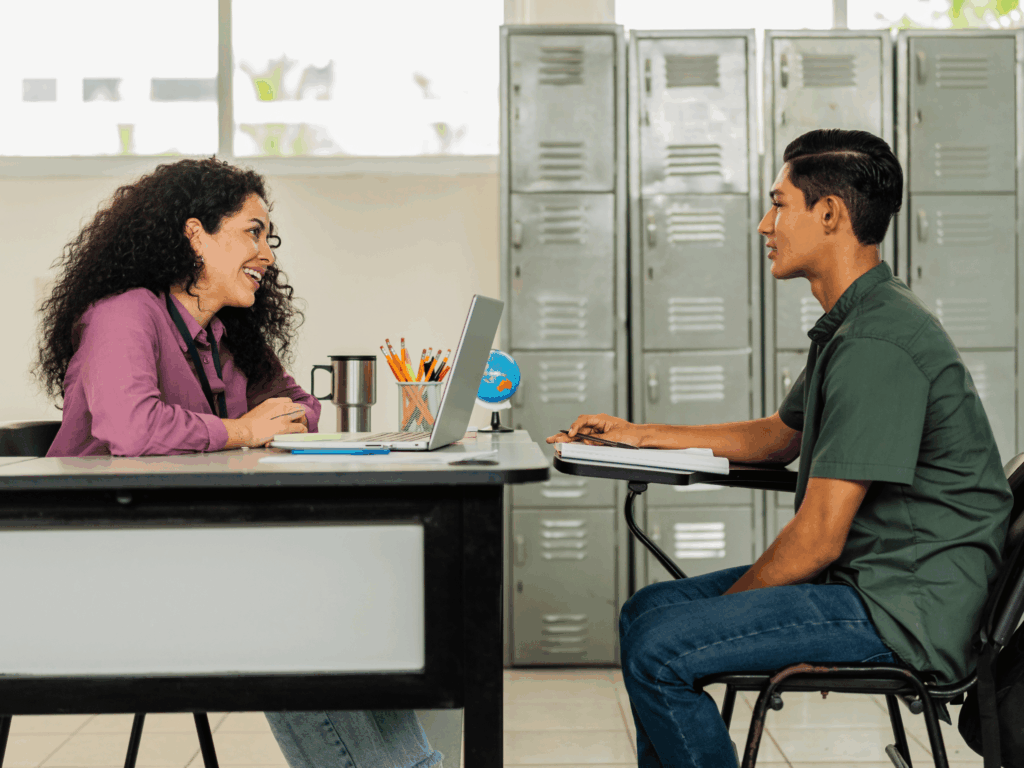
Discover how the New Albany Floyd County Consolidated School District secured its network and scaled access control in record time with <a href=”/portnox-cloud/”>Portnox Cloud</a>. Facing a diverse mix of 15,000 endpoints and limited IT resources, the district deployed Portnox Cloud across 20 buildings in weeks — not months — with real-time device visibility, seamless Chromebook integration, and no new hardware. The result: stronger security posture, simplified operations, and broad device coverage from day one.

Staying ahead in IT means strengthening cybersecurity—and zero trust architectures now lead the charge. But let’s face it: embracing zero trust can feel daunting. With so many tools and complexities, it’s easy to lose your way.
To understand how organizations navigate zero trust, Portnox teamed up with TechTarget. We surveyed hundreds of IT and cybersecurity professionals across North America. Discover the insights we uncovered in our Trends in Zero Trust report.
IEEE 802.1X authentication is a network access control standard that verifies user and device identity before allowing access to wired or wireless networks. It enforces port-based authentication, ensuring only authorized, policy-compliant endpoints can connect to enterprise infrastructure.
802.1X authentication secures both wired and wireless networks by enforcing identity verification at switches and wireless access points. This approach allows organizations to apply consistent access policies across all connection types, regardless of user location or device ownership.
A RADIUS server acts as the authentication authority in an 802.1X deployment by validating user or device credentials. It evaluates authentication requests against defined policies and determines whether network access should be granted, denied, or restricted.
802.1X authentication supports multiple identity verification methods through EAP, including usernames and passwords, digital certificates, and mutual authentication. Certificate-based authentication is commonly used to reduce credential theft, eliminate shared passwords, and support passwordless network access.
802.1X authentication supports zero trust security by enforcing identity verification before any network access is granted. It ensures no user or device is trusted by default and that access decisions are driven by authentication, policy, and security context rather than network location.
802.1X authentication secures IoT and unmanaged devices by combining standard authentication with alternative methods such as NAC-based authentication and segmentation. When paired with cloud-native NAC, organizations can enforce access controls even for devices that cannot run supplicants.
After completing the form, an email will be sent to you with the report download link.