Passwords were never designed to secure modern enterprise environments, yet many organizations still rely on them to control access across networks and remote users. Passwordless authentication solutions eliminate shared secrets entirely, verifying users and devices without passwords to reduce identity-related risk.
Portnox delivers a cloud-native, certificate-based passwordless solution that secures network access without agents, hardware appliances, or complex workflows. With automated certificate lifecycle management and 99.99% uptime, Portnox enables organizations to move beyond passwords while enforcing zero trust principles across every connection.

Passwordless authentication verifies user identity without relying on shared secrets like passwords or PINs, instead using cryptographic credentials or trusted devices that cannot be reused or easily compromised. Traditional passwords fail at scale—they’re routinely phished, reused, or exposed in breaches, creating security gaps and friction for both users and IT teams, even in MFA-protected environments.
While some passwordless methods rely on biometrics or hardware-backed credentials, certificate-based authentication is the most secure and scalable option for enterprises, replacing passwords with device-bound cryptographic identities that eliminate credential theft and enable continuous trust enforcement.
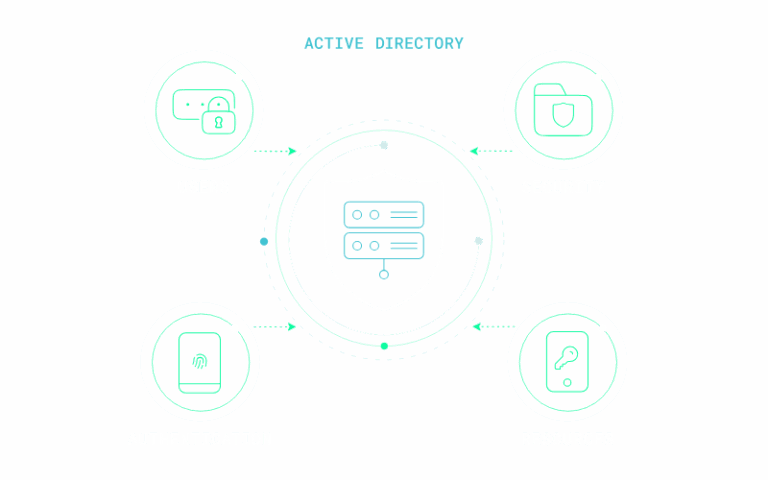
Portnox delivers certificate-based passwordless authentication through a fully cloud-native, agentless platform built for modern zero trust access management. Instead of relying on static credentials, Portnox uses identity-backed certificates to establish trust at the moment access is requested, continuously verifying users and devices based on identity, posture, and context.
By unifying NAC and ZTNA in a single platform, Portnox extends passwordless authentication across networks and applications without additional infrastructure or operational complexity. Trust is evaluated continuously rather than assumed, giving organizations stronger security, clearer visibility, and tighter control as access needs evolve.



Certificates vs. Passwords
Passwords are shared secrets that must be remembered, rotated, and protected. Certificates are cryptographic identities bound to devices and users. They cannot be phished, reused, or guessed, making them far more secure.
Comparing Passwordless Approaches
Biometric authentication and hardware tokens can improve user authentication for applications, but they often lack visibility into device posture and network-level enforcement. Certificate-based authentication binds identity directly to trusted devices and infrastructure, making it better suited for enterprise access control.
Certificate-Based Access vs. Push-Based MFA
Push-based MFA is vulnerable to fatigue attacks, SIM swapping, and OTP interception. Unlike approval-based workflows, certificate-based authentication eliminates user prompts while reducing the risk of unauthorized access.


Network Access (Wi-Fi and Wired)
Portnox enables seamless EAP-TLS authentication for 802.1X networks. Access decisions are enforced using identity, device posture, and role-based policies.
Remote Workforce and VPN Replacement
Certificate-based authentication enables secure, passwordless remote access without traditional VPNs by verifying user and device identity before any connection is allowed. When paired with ZTNA, access is granted based on identity, device posture, and context—supporting least-privilege access while maintaining visibility and control across distributed environments.
BYOD and Personal Devices
Portnox supports secure BYOD onboarding through self-service workflows that automatically issue certificates, enabling passwordless access without sacrificing device trust.
IoT and Unmanaged Devices
Agentless discovery enables Portnox to identify unmanaged and IoT devices, applying appropriate access controls and segmentation where applicable.
Extending this approach across environments improves overall identity security by ensuring access decisions are continuously validated, regardless of location or device type.


Portnox supports a wide range of enterprise use cases, including:


Passwordless authentication is no longer just an identity feature—it is a foundational control for modern access management. By replacing passwords with certificate-based authentication, organizations reduce risk, improve user experience, and strengthen security across every connection.


Staying ahead in IT means strengthening cybersecurity—and zero trust architectures now lead the charge. But let’s face it: embracing zero trust can feel daunting. With so many tools and complexities, it’s easy to lose your way.
To understand how organizations navigate zero trust, Portnox teamed up with TechTarget. We surveyed hundreds of IT and cybersecurity professionals across North America. Discover the insights we uncovered in our Trends in Zero Trust report.
Passwordless authentication is a security approach that eliminates traditional passwords in favor of stronger authentication methods such as certificates, device trust, or identity-based verification. With Portnox Cloud, passwordless authentication reduces credential theft risk while improving user experience by enabling secure, frictionless access based on verified identity and device posture rather than static credentials.
Yes, passwordless authentication is a natural fit for zero trust security. Portnox Cloud combines passwordless authentication with continuous device posture assessment and policy enforcement. Every access request is verified explicitly, and trust is never assumed based on prior authentication, ensuring access remains secure even as risk conditions change.
The most secure approaches eliminate shared secrets entirely. Certificate-based authentication binds cryptographic identity to trusted devices, making it more suitable for enterprise networks than biometrics or hardware tokens alone.
Passwordless authentication removes shared secrets and avoids common MFA weaknesses such as push fatigue and OTP interception. Cryptographic credentials cannot be phished or reused.
Portnox uses cloud-native onboarding with SCEP-based provisioning. Devices enroll automatically through self-service or MDM workflows, enabling certificates to be installed and renewed without endpoint agents.
Yes. Portnox enables secure BYOD access through automated enrollment workflows that issue certificates to personal devices while enforcing device trust policies.
Passwordless authentication supports compliance by reducing credential risk and enforcing device identity controls. It helps organizations meet requirements under HIPAA, PCI DSS, ISO 27001, and NIST 800-53.
After completing the form, an email will be sent to you with the report download link.