Defining response actions is a very important step in securing the company network. Here the security administrators will determine which specific actions will be taken for each type of event.
“Events” includes different scenarios, such as a rogue device connecting to the network, non-compliant devices connecting or an authenticated device connecting via an unusual access layer.
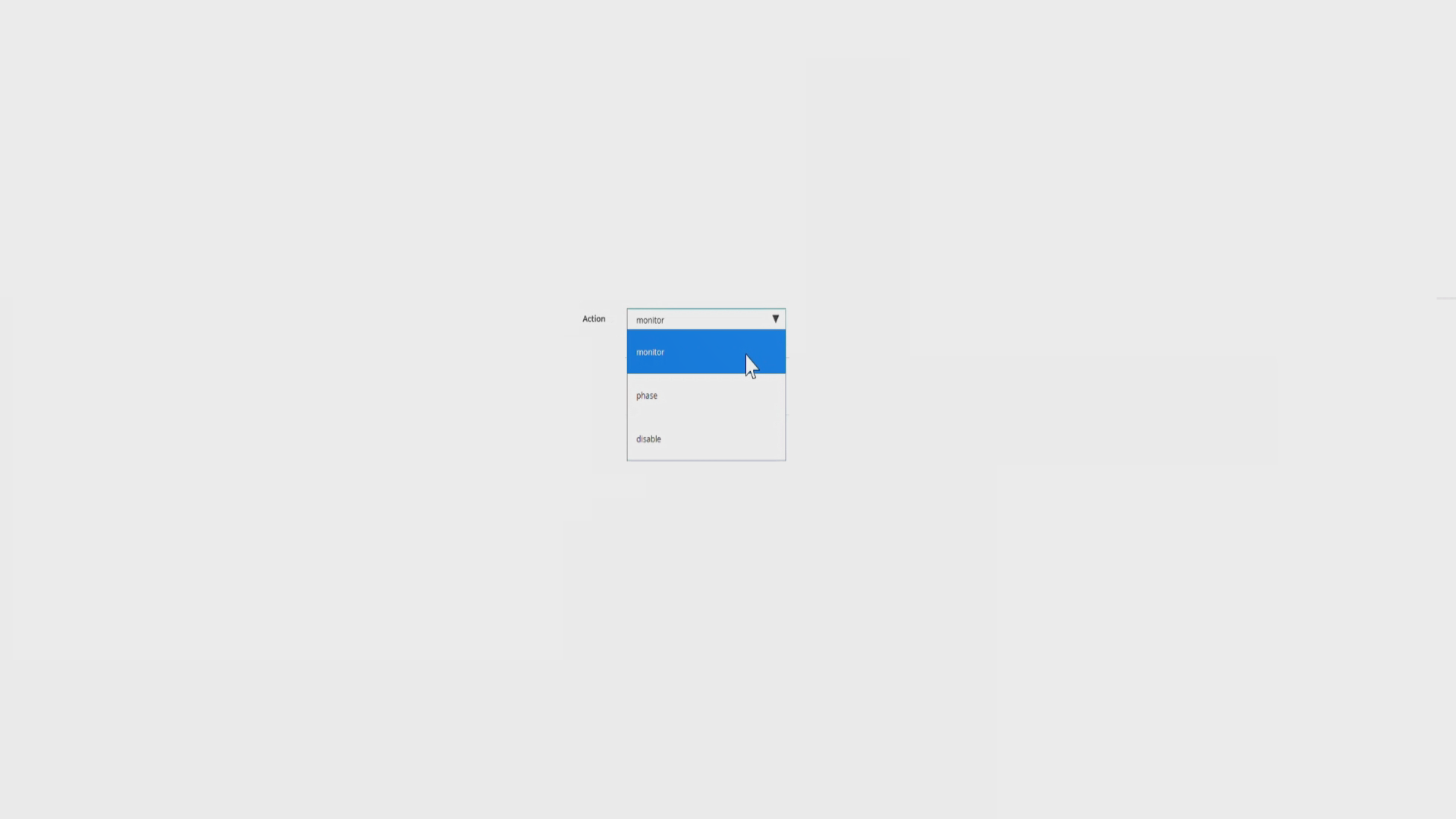
The response actions can be set to blocking a device from connecting to the network, quarantine or segmenting to a specified part or running a script on a suspicious device.
Please watch the following video to learn how to set up automated response actions:
Try Portnox Cloud for Free Today
Gain access to all of Portnox's powerful zero trust access control free capabilities for 30 days!