


Guest access allows non-employees—such as visitors, contractors, vendors, and partners—to connect to corporate networks without compromising security. With Portnox Cloud, guest access is securely managed through identity-based authentication, policy enforcement, and device visibility. This ensures guests receive only the access they need, while IT maintains full control and auditability across the network.
Portnox Cloud secures guest access by enforcing zero trust principles before granting network connectivity. Every guest connection is authenticated, evaluated against policy, and restricted to approved resources. Portnox provides visibility into who is connecting, from what device, and under which conditions—reducing risk from unmanaged or unknown endpoints without manual IT intervention.
Yes, Portnox Cloud automates guest access provisioning through customizable captive portals and policy-driven workflows. Guests can self-register or be sponsored, while access duration, permissions, and compliance rules are automatically enforced. This eliminates manual approvals, reduces IT workload, and ensures guest access is temporary, auditable, and aligned with organizational security policies.
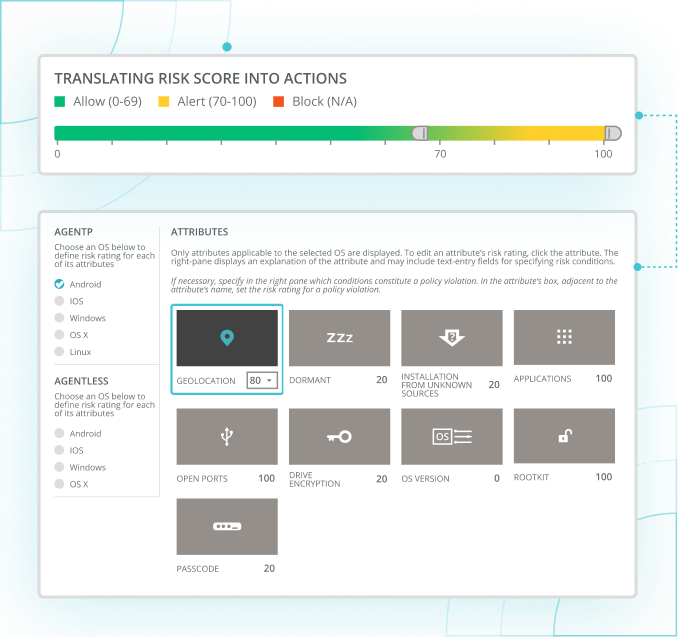
Portnox Cloud provides full visibility and control over guest and contractor devices connecting to the network. Devices are identified, classified, and continuously evaluated against security policies. Based on posture and risk, Portnox can allow, restrict, quarantine, or deny access—ensuring unmanaged or non-compliant devices never introduce unnecessary exposure.
Portnox Cloud supports agentless guest access, allowing visitors and contractors to connect using standard web-based captive portals without installing software. This simplifies onboarding while maintaining strong security controls. Agentless access is ideal for short-term users, BYOD scenarios, and environments where ease of access must be balanced with strict policy enforcement.
Guest access with Portnox Cloud reduces risk by preventing implicit trust. Guests are segmented from internal resources and granted only the minimum access required. Continuous monitoring ensures access can be revoked automatically if conditions change, helping organizations prevent lateral movement, unauthorized access, and compliance violations from guest and contractor connections.
Yes, Portnox Cloud is built to scale guest access across distributed and multi-site environments. As a cloud-native solution, policies are centrally managed and consistently enforced everywhere. Organizations can support guests, contractors, and partners across offices, campuses, and temporary locations without deploying on-prem infrastructure or managing site-specific configurations.
Your zero trust journey shouldn’t rely on disconnected tools.
Portnox Cloud delivers unified, cloud-native access control across users, devices, networks, and applications. One platform. One policy engine. No gaps. Just continuous, zero trust enforcement built for how enterprises operate today.
Cloud-native, posture-aware access delivering secure, passwordless connectivity to SaaS and private apps without VPN complexity.
Modern, cloud-based NAC securing wired and wireless access with instant device discovery, posture validation, and automated enforcement.
After completing the form, an email will be sent to you with the report download link.