What is a Dictionary Attack?
What is a dictionary attack?
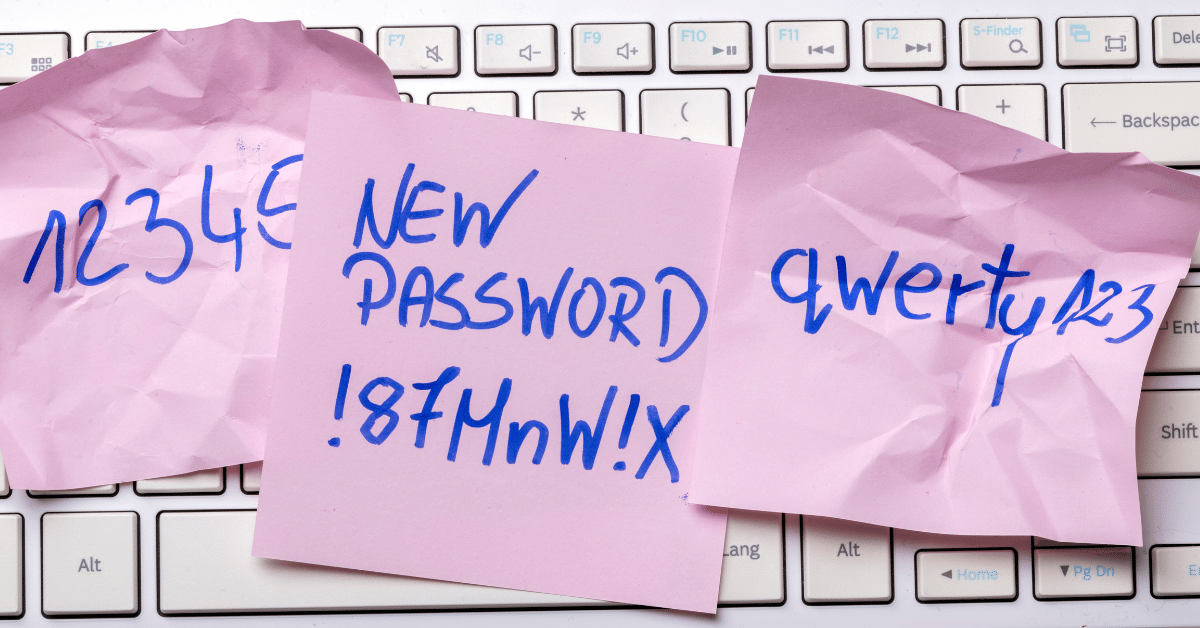
A dictionary attack is a type of cyber attack in which an attacker tries to gain unauthorized access to a user's account by systematically entering every word in a dictionary as the password. This method exploits the tendency of people to choose common words, phrases, or simple variations of them as their passwords.
In a dictionary attack, the attacker uses a list of words—typically compiled into a digital "dictionary"—which may include not only actual dictionary words, but also common passwords, phrases, and number combinations. The attack can be conducted against encrypted data, such as password hashes, or directly against an online account by attempting to log in with various password combinations.
To protect against dictionary attacks, it's recommended to use complex passwords that include a mix of letters, numbers, and special characters. Additionally, implementing account security measures like account lockout policies, which block access after a certain number of failed login attempts, and multi-factor authentication can significantly reduce the risk of such attacks.
How does a dictionary attack work?
A dictionary attack works by attempting to guess a password or decrypt a file using a pre-compiled list of likely passwords. Here's a detailed breakdown of how this process typically unfolds:
- Compilation of the Dictionary:
- The attacker compiles a list of potential passwords. This list can include words from an actual dictionary, common passwords, phrases, numbers, and possible combinations of these elements. Advanced dictionaries may also include common substitutions (like using '@' for 'a' or '3' for 'e') and variations.
- Target Identification:
- The attacker chooses a target, which could be an encrypted file, a password database, or an online account.
- Application of the Dictionary:
- For encrypted files or data: The attacker uses each word or phrase from the dictionary to attempt to decrypt the data. Each attempt involves using the dictionary word as a potential key or password. If the data decrypts correctly, the correct password is found.
- For online accounts: The attacker attempts to log in using each entry from the dictionary as the password. This is done through automated scripts or software that rapidly inputs each password attempt.
- Detection and Response:
- If the correct password is part of the dictionary, the attack will eventually succeed. The success depends on the comprehensiveness of the dictionary and the simplicity of the target password.
- Security measures such as account lockouts after multiple failed attempts, requiring captchas, or implementing delays between login attempts can interfere with or slow down a dictionary attack, making it less effective.
- Result:
- If the attack is successful, the attacker gains unauthorized access to the data or account. If not, and if appropriate security measures are in place, the attack may be detected and thwarted by the system's protective mechanisms.
Dictionary attacks rely on the assumption that many users choose weak or common passwords, making it statistically likely that simple, automated attempts using known data (like common passwords) will be successful. This method is less effective against strong, unique passwords or systems with robust security measures.
What is the difference between a brute force attack and a dictionary attack?
The main difference between a brute force attack and a dictionary attack lies in the approach and efficiency of how passwords are guessed:
- Approach:
- Dictionary Attack: This method uses a pre-arranged list of words that include likely passwords based on common words, phrases, common password habits, and popular substitutions. These lists are compiled from various sources, including dictionaries, leaked password databases, and common password conventions. The attack assumes that many users choose weak or common passwords, which might be present in the dictionary.
- Brute Force Attack: This method does not assume any knowledge about the password and attempts every possible combination of characters until the correct one is found. It starts from the simplest and shortest possibilities (like 'a' or '1') and moves to increasingly complex and longer combinations (like 'zzzz' or '9999').
- Efficiency and Speed:
- Dictionary Attack: Typically faster than brute force attacks because it only tests passwords that are more likely to be chosen by human users. If the user's password is a common word or phrase, it might be quickly uncovered.
- Brute Force Attack: Generally slower because it may have to go through millions or billions of combinations before finding the right one, especially if the password is long and complex.
- Success Rate:
- Dictionary Attack: More effective against passwords that are actual words or commonly used phrases and numbers. Its success rate drops significantly if the password is unusual or not included in the dictionary being used.
- Brute Force Attack: Guaranteed to eventually find the password, given enough time and computational power, because it tries every possible combination.
- Common Use:
- Dictionary Attack: Often used when there is some basis to believe that passwords might be simple or commonly used, such as attacking a database of user accounts where many users may have weak passwords.
- Brute Force Attack: More often used when other, less resource-intensive methods (like dictionary attacks) fail, or when the password is known to be long and complex, necessitating a comprehensive approach.
In summary, dictionary attacks are quicker and target weaker passwords, making them more practical for common scenarios. Brute force attacks, on the other hand, are more comprehensive but require significantly more time and resources, making them less practical for most scenarios but guaranteed to succeed eventually.
How can NAC help to stop a dictionary attack?
Network Access Control (NAC) can play a significant role in preventing dictionary attacks by controlling and managing device and user access to networks. Here’s how NAC can help in stopping such attacks:
- Endpoint Security Compliance:
- NAC solutions can ensure that all devices connected to the network meet specific security standards before they are allowed access. This includes having up-to-date antivirus software, which might detect and disable malicious programs used in dictionary attacks.
- Authentication and Authorization:
- NAC systems require devices and users to authenticate themselves before gaining network access. By integrating with stronger authentication methods such as multi-factor authentication (MFA), NAC makes it significantly more difficult for attackers to succeed using simple dictionary attacks on user accounts.
- Role-based Access Control (RBAC):
- NAC can enforce role-based access control, ensuring that users and devices only have the necessary permissions needed for their roles. This limits the potential damage that might be caused if an attacker gains access to a network using a compromised account.
- Monitoring and Logging:
- Continuous monitoring of network activity allows NAC systems to detect unusual login attempts or patterns indicative of a dictionary attack, such as rapid, successive login attempts. NAC systems can log these attempts and alert administrators who can then take immediate action.
- Proactive Response and Remediation:
- In the event of suspected dictionary attacks, NAC can automatically restrict or cut off network access for the affected accounts or devices, limiting the impact and reach of the attack. It can also trigger remediation processes, like forcing password resets or temporary account lockouts after several failed login attempts.
- Segmentation and Isolation:
- NAC can segment the network, isolating sensitive data and critical infrastructure from general access. This can prevent attackers who manage to gain initial access from moving laterally within the network to reach more critical systems or data.
By implementing these measures, NAC helps create a more secure and controlled network environment that is less susceptible to dictionary attacks and other types of unauthorized access. This not only prevents the immediate risks associated with dictionary attacks but also enhances overall network security against various threats.