In today’s world, high-security breaches face every sector, and the medical industry is no exception. The myriad of internet-connected medical devices and hospital networks designed for the improvement of health care services, also drive the increasing risk of security threats and vulnerabilities.
The US Food and Drug Administration (FDA) released several safety communications highlighting the vulnerabilities of connected medical devices. It is a known fact that eliminating cyberattacks is a near-impossible task – so manufacturers, hospitals, and medical practitioners must work together to manage risks. Naturally, the healthcare sector is a highly delicate environment. If cyber criminals access connected devices, the major target will be patient data.
A compromised medical device has the potential to cause severe injury or death. Therefore, it becomes imperative to align cybersecurity with patient safety initiatives. That way, there’s guaranteed protection for patient safety and privacy. It also ensures the continuity of high-quality service delivery without disrupting positive clinical outcomes. In recent years, the growth of the Internet of Medical Things (IoMT) has been a tremendous one. It has a projected $158b market value by the end of 2022, from $41b in 2017. Indeed, the IoMT is an integral and ever-growing part of the medical industry.
What is the Internet of Medical Things (IoMT)?
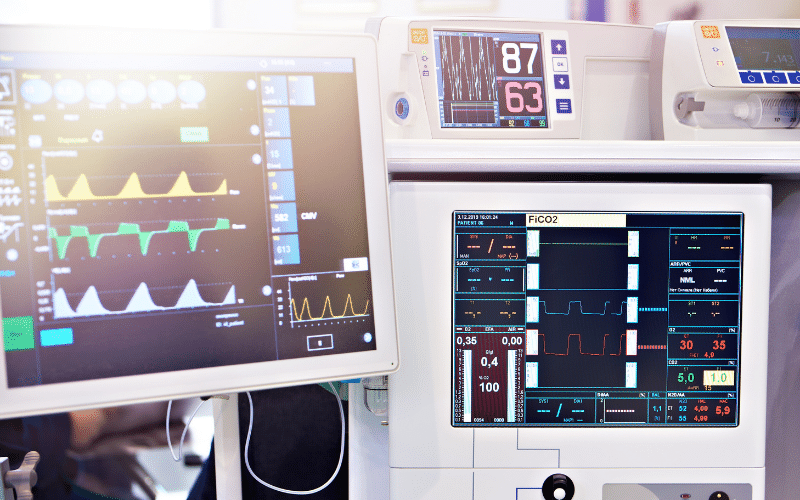
The Internet of Medical Things, also referred to as the Internet of Medical Devices (IoMD), is the network of medical devices and applications that connect to healthcare IT systems through the internet. Most medical devices with Wi-Fi functionality allow machine-to-machine communication of wireless and remote devices over the internet, allowing quick analysis of medical data. The sensitive nature and strict regulations surrounding healthcare data require extensive security infrastructure. Failure to keep patient data private comes with substantial penalties with regulatory bodies. Other impacts include losing access to medical records and the inability to care for affected patients. This all coincides with the undetermined reputational damage an organization might face.
Why is IoMT Important?
All connected medical devices store and process sensitive information. Most of the people associated here include caregivers, medical personnel, and patients. It is the very reason data protection mechanisms must take precedence in medical security. The major focus must be on sensitive data storage and any potential transmission risk.
Some of these risks to look out for include accessing locally stored data in memory, data transmission to other systems, and transmission of control information. Attackers focus on each point of these chains for malicious leakage. They target the most common transmission protocols to gain unauthorized access to health information. Once hackers discover a vulnerability in the system, it becomes their entry point to perpetuate malicious activities.
The importance of IoMT covers a broad scope, including in-home, in-hospital, on-body, the community, and more. People transmit medical data from home using a remote patient monitoring system. Medical personnel get to review and address minor issues of patients without having them travel to the hospital. This provides flexibility and reduces the re-admission of recently discharged patients.
IoMT covers mobility services such as tracking patients in transit for the community. It also includes the emergency response intelligence system to track patient metrics outside the hospital environment. On another hand, IoMT for in-hospital activities helps to track interactions for administrative purposes to understand the happenings within a the medical environment. Hospitals need to ensure that all connected IoMT have high security to guarantee the privacy and safety of data.
Another important aspect is wearable medical devices. On-body IoMT gets connected to monitoring systems for use outside the home or hospital. They ensure that people can go about their normal lives while still under medical observation. These devices track health metrics that get shared with healthcare providers. It becomes a matter of necessity to keep such data away from hackers.
Challenges With IoMD Security
Adopting the internet of medical things in healthcare is not smooth and seamless. As with every cybersecurity-related technology, it comes with quite a few challenges. Here are some that pose a nightmare to IT and cybersecurity experts.
Data Security Threats
One main area of vulnerability for hospital devices is legal technology. The machines in use have existed for over a decade before replacement. Many of these devices lack embedded security features that are up-to-date. For this reason, breaches can become highly susceptible to breaches by cyberattacks. Moreover, hackers know that an attack on a hospital network often involves prompt resolution. No medical facility wants to risk the lives of its patients, as compromise often leads to serious injuries. For facilities already using modern equipment, the interconnectivity of systems further increases the risk of data breaches, consistently putting healthcare IT teams on the frontline to prevent incidences that threaten patient safety.
High Costs
It’s not rocket science to conclude that ensuring the privacy and security of data comes with high infrastructure costs. The structure covers hardware, cloud computing, app creation, and more. Having to spend so much on all these IT infrastructures makes the adoption of IoMT a little challenging. However, it comes with good news – as there’s always a definitive return on investment
Interoperability
With high stakes comes high expectations. Data collection and collation are vital to getting relevant and meaningful clinical results. One major issue with IoMT is a medical device connection failure. There’s often a 45% failure rate due to issues like limited network capacity or physical limitations that can interrupt wireless signals. Therefore, it becomes imperative for all IoMT to have interoperability with one another so that every user can relay the data.
Regulatory Challenges
Medical device acquisition is never an autonomous decision. There is a need for approval and clearance from national regulatory bodies before a market launch. The IoMT often comes with contemporary challenges for regulatory authorities as well.
Human Error
Health care practitioners and patients alike should understand the added value of connected medical devices. More importantly, they must learn how to use them for better clinical outcomes. However, errors relating to passwords and other authentication activities could be the major source of exposure.
The Need For Improved IoMT Security
IoMT is the future of healthcare. Since both sensitive data and patient lives are at risk, medical establishments need an encompassing risk management strategy and utilizes every available method to ensure security. Without a doubt, there’s a great improvement in the health sector due to IoMT. Medical personnel receive more accurate data, give better diagnoses, and increase efficiency. It has also the improved patient experience by streamlining many processes.
First, risk assessment is a critical factor in understanding the location of the risk. It pinpoints these risks at each step in the chain of data and access. The next critical step is penetration testing and red team engagements. It gives experts an insight into real threat situations. With this knowledge, they get to implement and provide automated controls to detect potential access. Finally, the experts develop an effective risk management strategy to links all processes, which allows them to evaluate and improve the ever-changing security requirements.
Best Practices for IoMT Security
Despite the many security threats within the digital world, many IoMT devices still lack security. Healthcare providers need to put everything in place to avoid jeopardizing patient care. An organization can practice IoMT security and improve the healthcare sector.
Cyber Security Awareness
Security sometimes begins with the right education. It is often a challenge to present technology-related topics to healthcare personnel. Their major focus is on patient care and not IT issues. Therefore, it is a matter of necessity to get them well educated on cyber security best practices. Cyber security experts need to reiterate the need for the security of patient data. They also have to emphasize its role in improved health care.
Network Segmentation
Network segmentation is crucial for organizations already involved in the IoMT in order to help to separate patient data from the IT network. With this, detecting malicious activities and keeping patient information safe becomes easier.
IT Department
Most healthcare organizations see the IT department as just another non-medical department. However, the IT department is an integral part of the organization and must get treated accordingly. Their presence guarantees the security of ever patients’ information. In the event of a breach, activities get crumpled. Therefore, medical care professionals must ensure a consistent working relationship with the IT team while keeping tabs on cybersecurity medical device security issues.
Final Thoughts on IoMT
IoMT is the future of healthcare, and health organizations need to maintain the trust of both their patients’ health and the security of their protected health information (PHI) As the course to reduce cyber security advances in other sectors – the medical industry must be at the forefront.