The threat behind MAC spoofing
When implementing any insurance policy, you need to start with estimating the level of risk, the probability of that risk, and the potential damage should that risk become a reality.
One of the network risks that is often presented to demonstrate the ineffectiveness of 802.1x solutions is the ease of bypassing modern network access control (NAC) by using MAC spoofing. Usually, this involves spoofing the network printer or other vulnerable device.
Now, let’s put aside the fact that network printers today can support certificate or credential-based authentication, and that certain products have remedies against such attempts even when the authentication is based on MAC.
Let’s consider: is MAC spoofing a legitimate threat or an exaggerated, manageable flaw?
But before I try to analyze this risk, I want to point out the biggest advantage a NAC solution can give an organization to cope with modern cyber security threats: the ability to apply dynamic segmentation based on device type or identity.
Without going into too much detail, NAC is one of the only systems that can help you prevent lateral movement, indirectly allowing you to identify breaches and directly helping you to prevent the compromise of your crown jewels.
The threat landscape
Here are some of the most common adversaries when it comes to MAC spoofing:
- The employee – a disgruntled current or former employee
- The guest – a contractor, customer, patient, etc. who physically visits your organization for a period of time
- The hacker – a malicious person trying to attack your network and steal information, causing harm to your organization
And here are the most common attack surfaces:
- Wifi
- Wired, ethernet switches
One caveat: most wifi environments contain managed devices. So, for devices that do not have an 802.1x supplicant, and thus does not support certificate-based authentication (or credentials based), it is easy to setup an isolated segment and significantly lower the risk of attack.
As such, we’ll put our focus on examining wired environments, and how they’re vulnerable to the above adversaries.
Adversaries in-depth
Let’s be clear – MAC spoofing requires some technical knowledge to execute, which the non-technical lay person typically does not possess. Those doing it know what they’re doing, and they know it’s wrong.
With that said, it’s important to point out that a lot of damage is caused by the unintended – i.e. people clicking on a link in an email, deleting the wrong record or file, or even dropping a laptop into a pool.
The employee
Employees should be trustworthy. If they’re not, cyber security is likely not your problem. But, when someone is fired, laid off, or even just mistreated at work, there always exists the potential for them to hold a grudge. It’s human nature.
Disgruntled employees can pose a big risk. If an employee still works for an organization and he/she is determined to do damage, that’s a problem that’s nearly impossible to prevent. The network connection alone is not going to stop he/she from stealing data or worse. This individual likely already has access through other corporate devices and the credentials to access whatever data he/she wants.
At the end of the day, however, this individual’s risk of MAC spoofing can be categorized as “very low” with “low” probability and “low” potential for damage. The reason being is that the potential damage done is not necessarily related to network connection. The first line of defense against a disgruntled current of former employees is physical barriers – i.e. locked doors and other physical security.

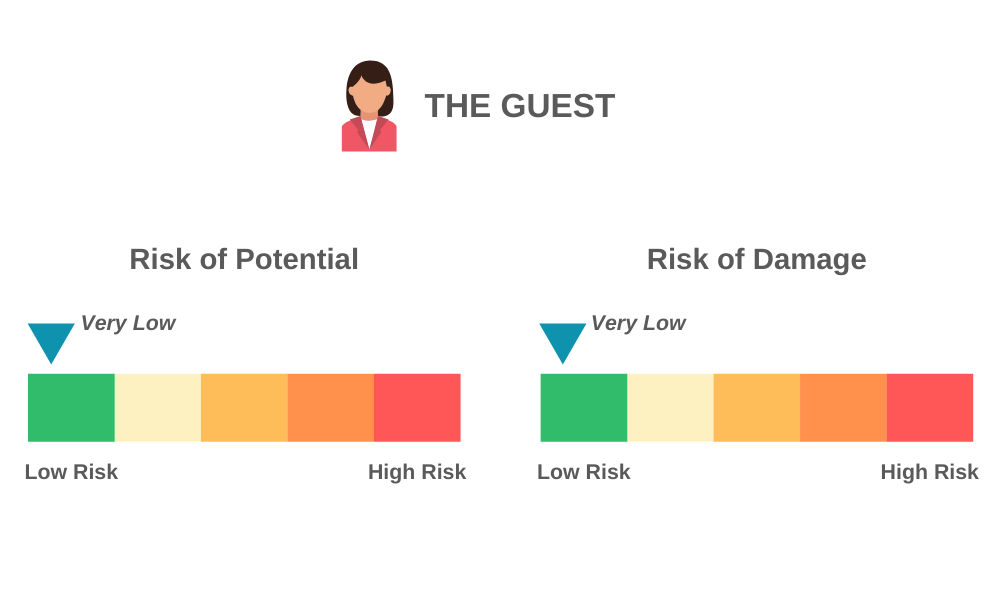
The guest
A guest visiting your office might want to connect to your network. Most likely, this guest will not go to great lengths to hack your network if they are initially blocked. By supplying a guest network, such as a guest wifi, you will effectively eliminate that risk all together. Thus, like the employee, this individual’s risk of MAC spoofing can be categorized as “very low” for both probability and damage.
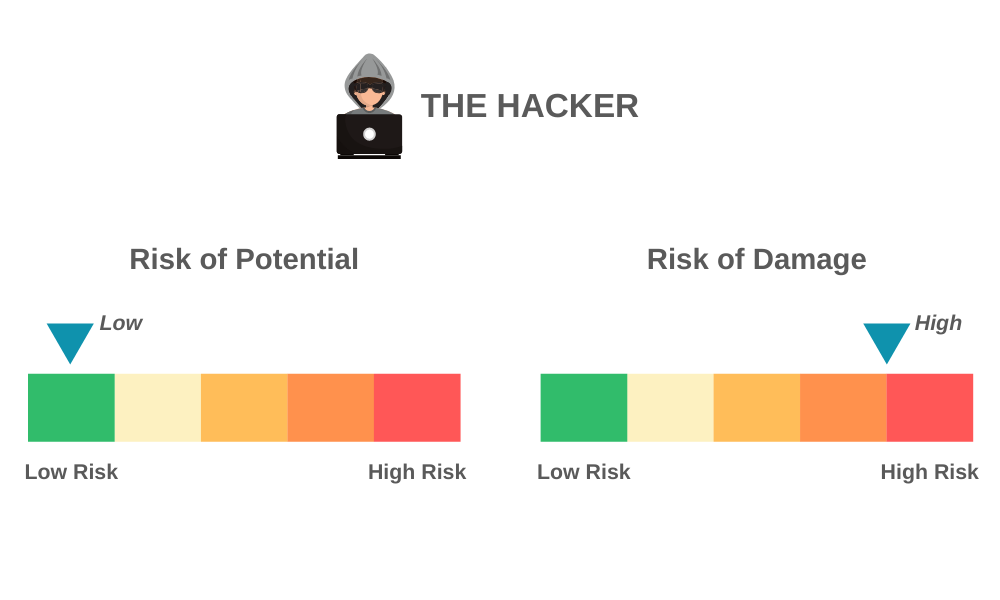
The hacker
A hacker will need physical access to your network in order to do his/her job. Today, spearhead attacks can enable hackers to access your networks from afar. Doing so, however, typically requires some sort of motive.
This motivation is often dependent upon the type of business you operate. If you’re in military and defense, for example, you likely have a higher than average risk of being the target of such an attack. The same going for banking and financial services, healthcare and any other industry with highly sensitive and confidential data.
For most organizations, the threat of physical access hacking is typically low, while the potential for damage could be high. Should a retailer fear physical burglary just because a new device has connected to its network? I think not.
In conclusion
For most organizations, the risk of MAC spoofing is almost non-existent. This is usually fairly easy for an auditor to demonstrate, and would appear as part of a comprehensive security report. So in reality, the perception of the threat is that it’s a much larger problem than it actually is.
You can also prevent MAC spoofing by implementing stronger authentication methods that are fairly common today. One of the major roles of NAC is to provide secure authentication and authorization to the network. Thus, even if authentication is somehow breached, authorization serves as a second layer of defense that can limit access by putting potential individuals of risk in a specific “narrow” segment.
The segmentation of specific types of MAC-based devices is a best practice in NAC. Even if spoofing occurs, such a device won’t be able to access a particularly sensitive VLAN, such as those in Finance or HR, if proper segmentation has been established through your network security policies.
