Why MFA Isn’t Going to Save You
Think multi-factor authentication (MFA) is iron-clad protection against a data breach? Think again. Hackers are increasingly coming up with clever ways to bypass MFA, from social engineering to elaborate man-in-the-middle attacks. Here are some of the ways bad actors exploit MFAs:
One-Time Passcodes
The worst form of two-factor authentication is the one-time passcode (OTP). Not only are the passcode text messages annoying, but they are also not very secure.
SIM Swapping
Even if your phone never leaves your pocket, hackers can get control of all your digital life by a technique known as SIM swapping. A Subscriber Identity Module (SIM) is a little card from your phone carrier that stores information to point your phone to the correct cellular network to pick up your correct phone number, and other information to identify it. Nowadays most smartphones use eSIM, which is a digital version of what used to be a physical card. Since it’s now all electronic, all you need to do to change things around is call your cellphone provider. If a hacker gets enough information about you – often through a phishing text message, or just scraping social media – they can call your carrier and change your number to their phone. All OTPs will then go to their phone instead of yours, letting them reset accounts and gain access to even more information. Think this is unlikely? The former CEO of Twitter begs to differ.
Provider outage
On February 22nd, 2024, US cell provider AT&T suffered an outage impacting 74,000 subscribers for approximately 12 hours, starting at 3:30am ET. Beyond just a frustrating inconvenience, if you use SMS one-time passcodes for MFA, you were not able to receive messages for the majority of the workday. Unfortunately, AT&T is not the only carrier to have issues – Verizon customers also reported wide-spread connectivity issues for at least 4 hours on January 26th, 2024. T-Mobile users were lucky this go-round, but maybe that’s because they had their turn in February of 2023.
SMISHING
This is a silly word for a serious problem; phishing via SMS. Text messages are easy to fake; If your employees are used to getting authentication messages via SMS, it’s that much more likely that they’ll click on a bad link in a moment of carelessness. It happened to Activision in 2022; several employees got fake text messages, and only one person fell for the scam, but that was enough. The victim, in this case, happened to be part of HR, which gave the hackers access to quite a bit of data.
Passcodes Are Not Randomly Generated
You probably haven’t given much thought to how one-time passcodes are generated, but there is a vague assumption that when a request is made, some server farm somewhere generates a random number and sends it out to you, and then deletes it after you successfully log in. That makes sense, but you’d be wrong. The codes are, in fact, stored in a database. YX International, a company that serves OTPs for multiple big-name companies like Facebook and Google discovered this database was left wide open for anyone to access. Thankfully, it was found by a security researcher who alerted the company. Next time, it may be someone with significantly less altruistic motives.
We’ve established that OTPs have got to go. Maybe authenticator apps are the solution? They are more secure, they solve many of the issues above like carrier outages and stolen phone numbers, plus phones are protected with biometrics so hackers will need to physically take the phone to do any damage, but they aren’t as safe as you may think.
MFA Fatigue
When you use an authenticator app, signing in often prompts a push notification to approve or deny access. Hackers will bypass this issue by spamming your device with repeated push notifications in the hopes that you’ll approve, either to make it go away, or by accident (we’ve all clicked “Next” when we meant to hit “Cancel” after all.) Cisco was hacked using this method after an employee’s Gmail account was compromised. Sometimes there is a social engineering component –as was the case when Uber was hacked in 2022., The hacker contacted the owner of the compromised account and pretended to be from Uber’s IT department and asked them to approve the notification.
Attacker-in-the-Middle (AiTM)
This attack is somewhat complex, but is also becoming disturbingly more common. An attacker sets up a fake website that mimics a legit one – such as a banking portal, or an internal portal. They launch a phishing campaign that directs customers and/or employees to the fake site. They use this site to capture credentials and redirect to a fake MFA site, where the user puts in their real prompt – which the attacker then passes on to the real website and captures the session cookie while the “fake” site sends the user elsewhere.
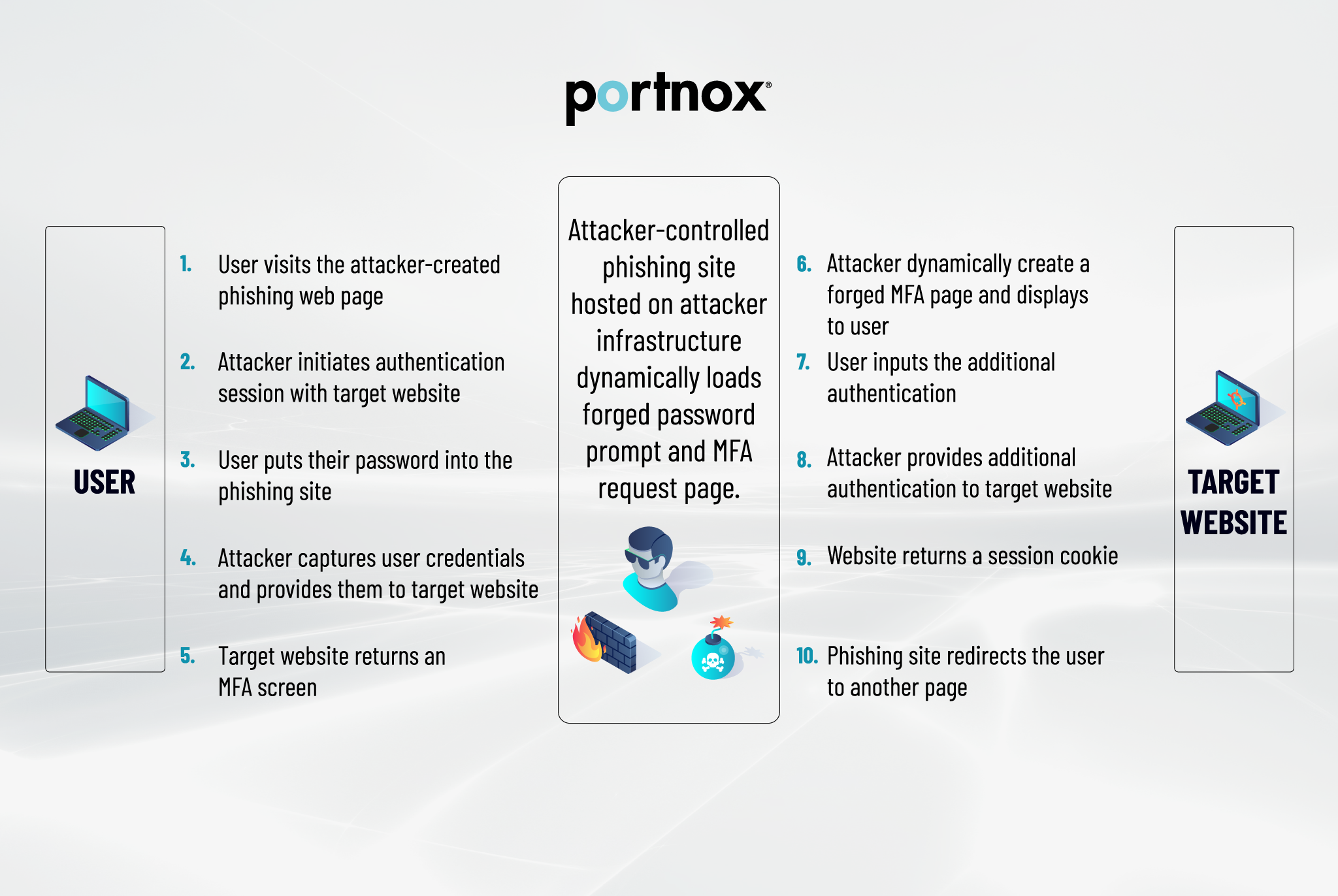
Microsoft uncovered a huge AiTM attack in 2023 aimed at financial institutions, and Reddit was hacked that same year using a similar method.
Stolen Cookies
There are almost as many varieties of this attack as there are of actual cookies: pass-the-cookie, cookie poisoning, cookie tossing – but they all boil down to the same basic concept: Once you log in to something through a web browser, a cookie file is created that tracks your session. Without this, you’d have to log in to each page of a website individually, which would make online banking possibly the most frustrating exercise on the planet. Our ever-expanding portfolio of cloud-based services makes these cookies an extremely attractive target. Successful manipulation of a session cookie completely bypasses MFA. When Okta was hacked in 2023, the hackers went after support files, which just so happened to gather cookie information, and was also a factor in the 2020 SolarWinds data breach.
MFA is Inconvenient
You may not think inconvenience is relevant to how MFA can be bypassed, but consider this: Microsoft was hacked in November 2023, and the hackers used a simple password spray attack to compromise e-mail accounts of top executives which didn’t have MFA turned on because no one wants to get a code or approve a push 20 times a day. In response to the Okta hack, the company announced it would be turning on MFA for protected actions in their admin console. Why wasn’t it on before? Because it slows you down, interrupts your workflow, and is generally annoying. This creates a tendency not to enable it everywhere, which can leave dangerous gaps in your security. The worst part of all of this is, it’s not terribly difficult or complex to do. There are resources available that will show you how to deploy each of these hacking strategies.
Passwordless Authentication is the Future
You may have noticed a recurring theme through these breaches – some form of phishing and/or social engineering is effective when you want to bypass MFA. With the thousands of hours of training, fake phishing e-mail tests, and articles published on security best practices, the reality is that passwords are inherently weak, because they still rely on a human element, and the best way to really keep yourself, your data, and your entire organization secure is to remove that element entirely. Switching to certificate-based, passwordless authentication eliminates all of these issues because certificates are encrypted – they can’t be guessed, phished, or socially engineered. And in a rare win for anything that enhances security, certificates provide a better user experience because there’s no password to remember, no passcode to get from a text message, and no push notifications. Make everyone’s daily digital life easier and more secure with passwordless authentication! Portnox’s cloud-native NAC solution delivers passwordless authentication, endpoint risk monitoring, and 24/7 compliance enforcement.If you look up NAC solutions on Reddit, you’re likely to encounter frustration, anger, and genuine sadness. That’s how users feel about archaic and cumbersome legacy NAC products. That sorrow ends today. With the Portnox Cloud, powerful and easy-to-use network access control functionality is available at your fingertips.
