FIPS (Federal Information Processing Standards) is an umbrella term for several standards relating to specific security concerns (for example, FIPS-201-2 refers to personal identity verification for federal employees). FIPS 140 is a set of standards governing cryptographic modules – basically, anything that encrypts data, be it hardware or software. The Portnox Cloud’s zero trust NAC is a perfect solution to help cover FIPS-140 compliance requirements for your organization.
The core function of NAC is to enforce access control policies by authenticating and authorizing devices and users before granting network access. It verifies the identity and security posture of devices, ensuring they meet the necessary security requirements before being allowed on the network. The Portnox Cloud allows you to control access based on role, location, device type, and many more options.
NAC solutions can enforce encryption and secure communication protocols to protect data in transit. By ensuring that devices comply with encryption standards and secure communication protocols, NAC helps meet the encryption requirements of FIPS 140. The Portnox Cloud utilizes 802.1X along with EAP-TLS to encrypt all communication from us to you and back again, so you can rest assured your data is secure in transit.
NAC solutions can enforce endpoint security policies so that you can ensure security measures like keeping anti-virus up to date or running a firewall are always in place. The Portnox Cloud’s offers a robust risk policy and compliance engine that covers a broad scope of endpoints and criteria – from passcodes on phones to registry entries on Windows. We also offer automated remediation options, so your devices can be brought into compliance without any action from your IT admins.
NAC systems typically provide continuous monitoring capabilities, allowing administrators to track and analyze network traffic, user behavior, and device compliance. This helps identify potential security incidents or policy violations promptly, supporting the continuous monitoring requirements specified in FIPS 140. The Portnox Cloud continuously monitors the risk score of connected devices, so that if something changes post-connect immediate action can be taken either by IT or by our robust automated remediation service.
FIPS 140 requires comprehensive reports on network access, device compliance, and security incidents. This serves to not only keep IT admins on top of any potential access threats, but these reports can help organizations demonstrate that they have evidence of access control measures, encryption usage, and security posture. The Portnox Cloud offers a variety of reporting and alerting options that can generated on-demand or regularly scheduled.
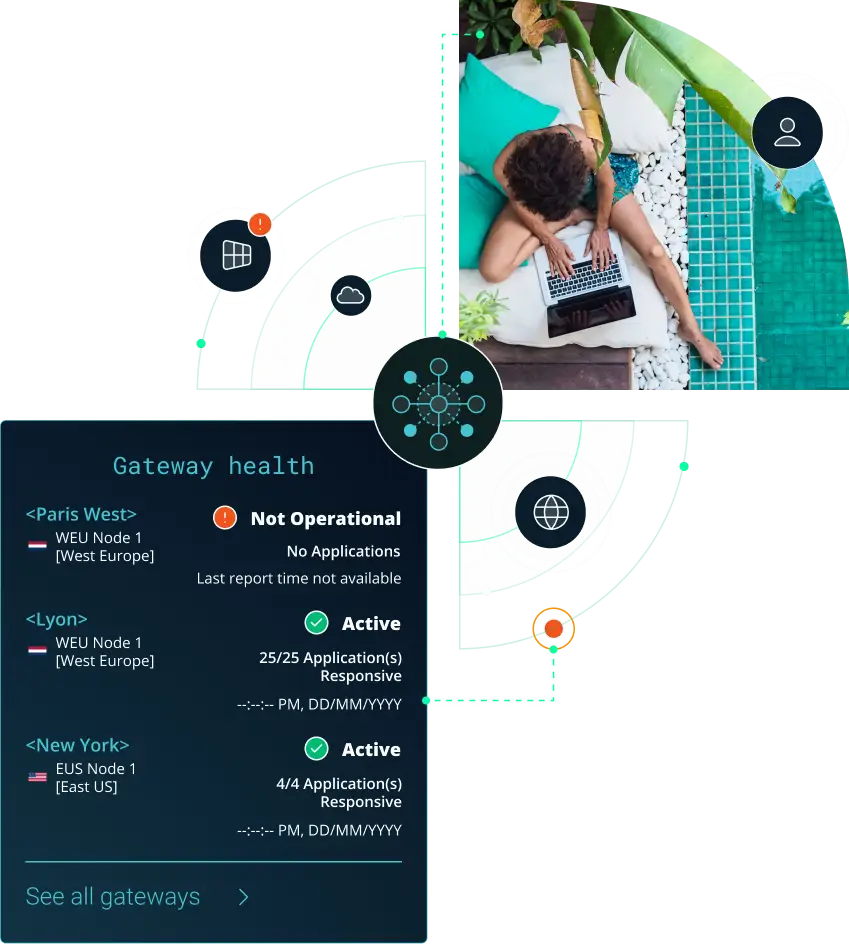
The Portnox Cloud has been purpose-built to easily enhance your remote access security for your workforce connecting via virtual private networks (VPNs) with full endpoint risk awareness and access controls. Put simply, Portnox delivers remote access control as a cloud service.
FIPS 140 compliance refers to meeting the U.S. government standard for cryptographic security, formally known as FIPS 140 (Federal Information Processing Standard). It defines requirements for cryptographic modules used to protect sensitive information through encryption, hashing, and key management. Portnox Cloud supports FIPS 140 compliance efforts by enabling secure, policy-driven access control that aligns with strong authentication and encryption best practices.
Portnox Cloud supports FIPS 140 compliance goals by strengthening identity-based access control and enabling certificate-backed authentication for network access. This reduces reliance on weak credentials and supports secure cryptographic trust for devices and users. By enforcing centralized policies and continuous posture checks, Portnox helps organizations maintain stronger control over access to sensitive systems and protected data.
Certificate-based authentication supports FIPS 140 compliance by using cryptographic credentials rather than passwords to verify device and user identity. Portnox Cloud enables certificate-based onboarding and enforcement for network access, helping reduce phishing risk and credential theft. This approach aligns with organizations that require high assurance authentication and cryptographic validation to protect sensitive information
Yes. While FIPS 140 compliance is focused on cryptographic modules, network access control supports compliance objectives by ensuring only authorized, trusted endpoints can connect to protected networks. Portnox Cloud enforces NAC policies using identity and device posture signals, reducing exposure and preventing unauthorized connections that could compromise systems relying on validated cryptographic protections.
After completing the form, an email will be sent to you with the report download link.