MoveIt Cyber Attack Impacts DOJ, Pentagon Networks
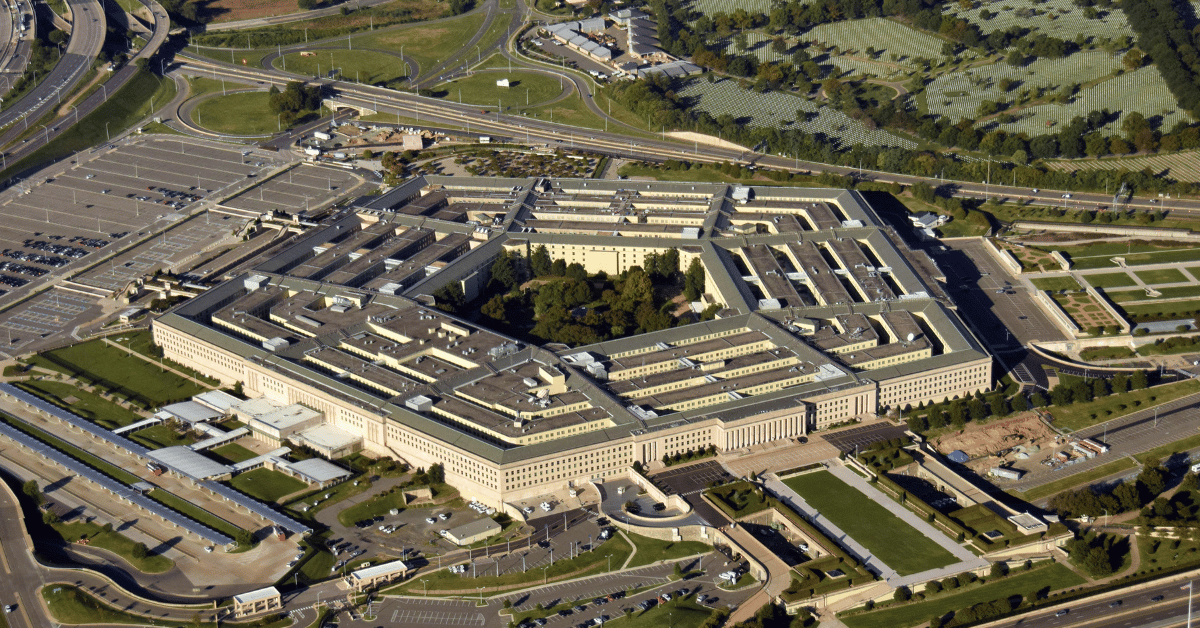
A major cyberattack on MoveIt, a medical imaging file sharing platform, recently impacted government networks at the Department of Justice (DOJ) and Pentagon. While investigations are still ongoing, the breach highlights risks when third-party vendors like MoveIt gain extensive access to sensitive systems. On October 3, MoveIt disclosed that unauthorized third parties breached their network and gained access to customer files. The cloud platform is used by healthcare organizations to share medical images and documents. Customers impacted include the DOJ and Pentagon, which utilize MoveIt to securely exchange files with external medical facilities.
Attackers were able to access imaging files associated with government employees and their dependents receiving healthcare services. Exposed records contain sensitive personal information including names, ID numbers, birth dates, and medical history. It is unknown precisely when the attackers first infiltrated MoveIt’s systems. Evidence suggests possible access extending back several months. The incident was discovered by MoveIt cybersecurity staff on September 15. However, the breach was not reported publicly until October 3. This delay allowed attackers ample time to explore internal MoveIt networks undetected. During this period, they retrieved login credentials to systems of multiple MoveIt customers, including the DOJ and Pentagon.
With this access, the attackers were able to infiltrate further into government networks and download additional files beyond just medical images. The full extent of the data theft remains under investigation by federal cybersecurity teams. So far, it is believed several thousand DoD and DoJ files were exfiltrated by the attackers prior to their activity being discovered. Investigators have not yet confirmed whether this included classified documents. The culprits behind the breach have not been identified publicly.
NAC’s Role in Reducing the MoveIt Cyber Attack
Cybersecurity experts state implementing network access control (NAC) could potentially have reduced the breach impact. NAC solutions provide visibility into all network activity and allow granular access control policies to be enforced. With NAC, the DOJ and Pentagon could have detected unusual access patterns from MoveIt much quicker. Restrictive policies would also limit what data MoveIt could retrieve from government networks. Any unauthorized activity would be flagged and blocked by the NAC system. Additionally, NAC would make lateral movement across networks more difficult even with stolen credentials. The continuous monitoring and microsegmentation capabilities would contain attackers to small network segments.
Government agencies frequently share access to internal networks with third-party partners and vendors. The MoveIt cyber attack exemplifies the immense risks this poses if robust security controls aren’t implemented. Perhaps most concerning is that warning signs may have been missed. MoveIt had previously reported separate security incidents earlier this year involving potential network compromise. Despite this, the DOJ and Pentagon took no action to limit MoveIt’s access to sensitive systems. This highlights the critical need for continuous third-party vendor risk assessments. Government agencies must regularly audit partner security measures and enforce least privilege access. Potential red flags need to be addressed quickly, not ignored.
As cyberattacks grow more frequent and advanced, the federal government must prioritize modern security tools like NAC and zero trust architectures. Outdated perimeter defenses are inadequate. Protocols allowing third-party access require greater scrutiny along with internal network monitoring. The MoveIt cyber attack of DOJ and Pentagon networks will likely result in Congressional hearings and DOD/DOJ policy changes. But real-world impact on national security remains unknown as investigations unfold. Ultimately, the MoveIt cyber attack serves as an urgent wake-up call for improving cyber defenses across both government and the healthcare sector. Tighter access controls and network visibility would be a good start.