As your organizational threat surface grows in size, scope and complexity, the adoption of cloud security tools is key to maintaining a secure status quo.

Cloud adoption is an IT security strategy that is disrupting industries around the world. The move to the cloud provides convenience, lower total cost of ownership, and consistent uptimes compared to on-premises infrastructure. As a result of the benefits available from cloud migration, it’s expected that spending on public cloud infrastructure and services will grow to $500 billion by 2023.
When it comes to cybersecurity, cloud security (or cloud computing security) spans policies, practices, and technologies for protecting cloud computing systems. In essence, cloud security fundamentally secures cloud-stored data and other digital assets against data breaches, malware, distributed denial of service (DDoS), hacking, and other cybersecurity threats.
With cloud security, end-users expect their data to be more secure in the cloud than on their hard drives or local servers. Though cloud service providers have cybersecurity measures in place, that doesn’t mean they are invulnerable to data breaches, DDoS, and other cybersecurity threats.
So, why is it that so many companies are turning to the cloud, particularly for security? Well, the this questions yields a variety of interconnected answers:
In general, companies can’t take advantage of the many benefits of the cloud while maintaining their security posture without adequate security measures for cloud-based applications and a growing volume of data residing in the cloud.
Traditionally, networks had no means of ensuring that its servers were fully protection. Today, with cloud web security, traffic gets to the cloud instead of being routed to the servers directly. The cloud analyses the traffic and only allow the legitimate users to gain access. Any traffic that the cloud does not approve, it blocks it from getting to the server.
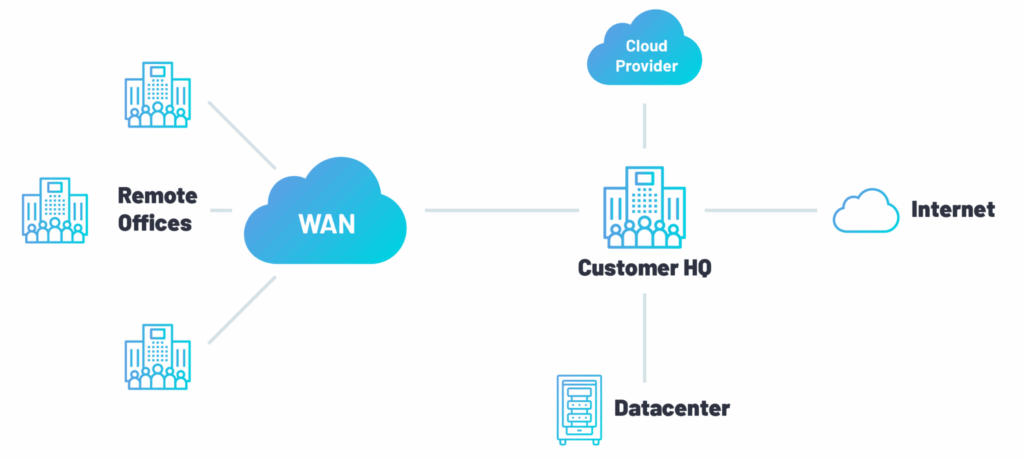
On-premise applications filter data before it reaches the server, often making them hard and costly to maintain over time. They filter traffic after it reaches its network. Sometimes the machines get overwhelmed and may shut down to block both good and bad traffic, and they may not serve the intended functions. With cloud security solutions, traffic is typically redirected to the security cloud first, where it gets filtered before reaching the respective application.
Nearly primary management and productivity tool used by businesses have shifted to the cloud. Network access control is no exception. The inherent productivity, operational, economic, and accessibility benefits have driven this trend in the last fifteen years. When it comes to NAC, however, there is a big difference between cloud-based and cloud-delivered.
Today, almost all NAC vendors offer an accessible cloud-based (or managed) platform from which to manage network access, but this typically still requires on-site hardware to be installed. A cloud-hosted NAC environment is generally the “on-premise” software hosted on dedicated servers and managed by the vendor on behalf of the customer. These are effectively on-premise applications that are available remotely.
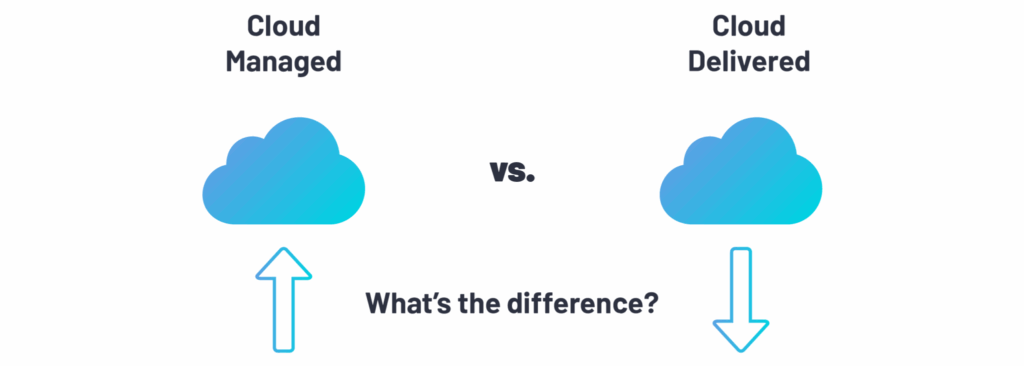
Contrary to cloud-based applications, cloud-hosted applications are generally not designed to be hosted as multi-tenant instances and can come with several challenges:
With a cloud-delivered approach to NAC, however, you stand up everything from a RADIUS server in the cloud to allow for centralized authentication and authorization up to certificate authority, resulting in:
As we move into the 2020s, you can expect to the cloud native security platforms (CNSPs) market to expand. These platforms will enable cybersecurity teams to manage all of their security across public, private and hybrid clouds from a single console. Siloed security solutions will be integrated into these comprehensive platforms: capabilities such as network access, governance and compliance, threat detection and response, data loss prevention and beyond will all live in a single pane of glass.
As multi-cloud strategies grow in popularity, we’re seeing an increase in visibility issues. Moving forward, cybersecurity teams will continue to search for ways to gain the level of visibility they once enjoyed on-premises. Traditionally, cloud native resources have made visibility difficult, but new security platforms that leverage proprietary cloud provider APIs offer richer context for cloud-based workloads.
SASE, pronounced “sassy”, stands for Secure Access Service Edge. It is a cloud-based network security model and category, proposed by Gartner in 2019, to support agile secure access to enterprise assets. This model includes the network security solutions in a global and cloud-native service that allows IT teams to easily connect and secure all of their organization’s networks and users in an agile, cost-effective, and scalable way. This is especially useful in the currently globally dispersed digital enterprise.
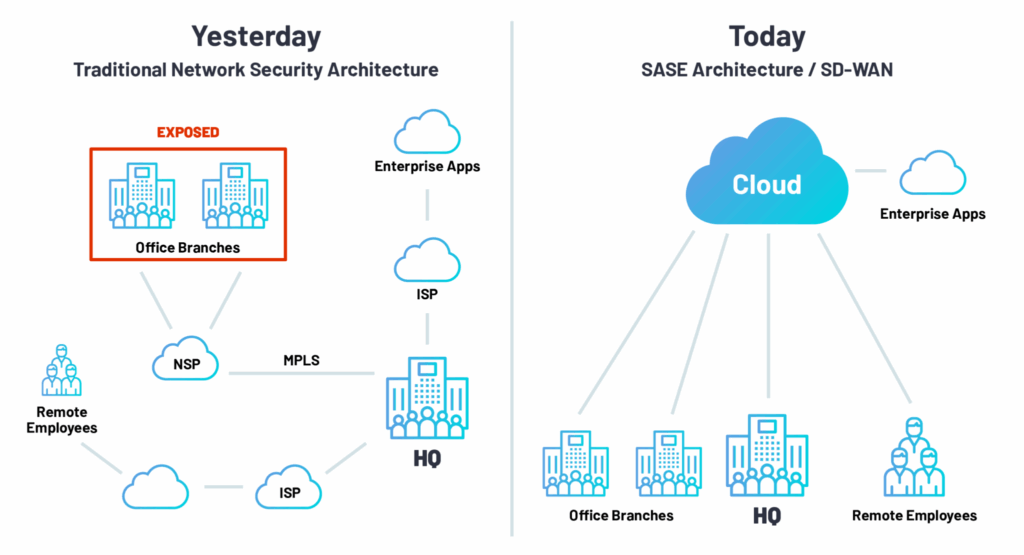
The sensible course of action is to plan a security strategy to be scalable and efficient in the present, while at the same time future-proofing the organization’s security. With the organizational data migrating to the network edge, it makes sense to authenticate and authorize users and devices in a cloud format, thereby assuring that regardless of the equipment and geolocation, employees can securely connect in a cost-efficient and secure method to the needed resources.
After completing the form, an email will be sent to you with the report download link.